The Internet is no more a secure place. Everyone is continuously being tracked, and the user’s data is being shared with several advertisement services.
Luckily, a virtual private network or often abbreviated as VPN can help you resolve the issues mentioned above.
If you were scouting for some of the best VPN services, then this article will help you. In this article, we have shared some of the best free and paid VPN services.
RELATED: Is your VPN 100% secure?
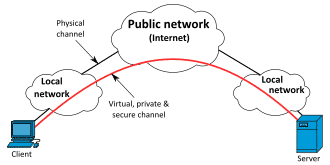
What is a VPN?
According to Wikipedia, A virtual private network (VPN) extends a private network across a public network. It enables users to send and receive data across shared or public networks as if their computing devices were directly connected to the private network.
In simple words, a VPN enhances protection and offers improved privacy while you’re browsing the internet. In addition to improved privacy, a VPN might also help you in accessing websites and services that are blocked in your region.
How does a VPN work?
Before sharing the actual list of best free and paid VPN services, it’s essential to know how does a VPN work.
You can consider VPN as a tunnel that directs your device’s internet connection through its private server and then transmits your data to the internet.
A VPN ensures that your origin never gets revealed, and it does so by hiding your IP address.
Best Free VPN Services For 2020
1. Speedify
Speedify is a feature-rich VPN service, and as its name recommends, it’s pretty fast. This free to use VPN uses channel bonding technology, which combines multiple Internet connections to provide increased bandwidth couped with lower latency.
The next major highlight of Speedify is its security. Well, Speedify uses ChaCha or AES-based encryption algorithm to safeguard your data against hackers.
Speedify boasts more than 50 server locations, and it offers around 5GB of data each month for free users. You can upgrade this data limit by getting the Speedify subscription.
2. TunnelBear
The next best VPN service on the list is TunnelBear. Now owned and operated by McAfee, TunnelBear allows users to browse the internet from 23 countries.
This free VPN service uses a secure AES 256-bit encryption.
The free version of TunnelBear offers around 500MB of traffic each month. However, you can upgrade to a paid subscription to increase the data limits and remove country restrictions.
In addition to desktop clients, TunnelBear also has its native Android and iOS client. Overall, TunnelBear is a great VPN service that simply gets the job done.
3. SurfEasy
If you use the Opera web browser on a regular basis then SurfEasy is the best free VPN service for you.
As you might now, SurfEasy comes bundled with the Opera web browser. Even after being a free VPN, SurfEasy can be used on five devices simultaneously.
Furthermore, SurfEasy offers around 500 ultra-fast servers spread across 25 countries.
As for downsides, SurfEasy only offers a monthly data limit of 500MB. Though, it is worth noting that if you are using the integrated version of this VPN on the Opera web browser then there’s no data limit.
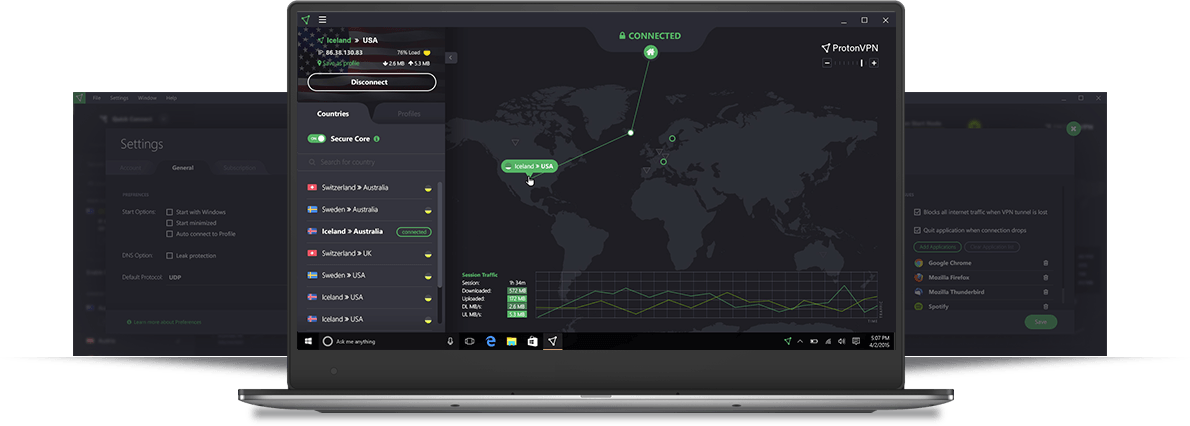
4. ProtonVPN
ProtonVPN is another free yet reliable VPN service. This popular VPN service encrypts your network traffic with AES-256.
The free subscription of ProtonVPN offers access to three countries and it can be used on only one device. Moreover, the speed on the free plans is a bit slower in comparison to the paid plans.
PtotonVPN has around 610 servers spread across 44 countries.
Unlike the other free VPN services on the list, ProtonVPN doesn’t impose any bandwidth limits. As a result, you can use as much data as you want.
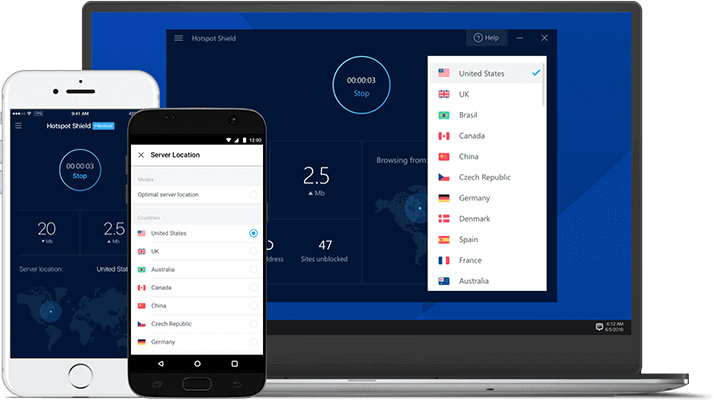
5. Hotspot Shield
The last free VPN service on the list is Hotspot Shield. This free to use VPN service offers military-grade encryption and it’s available for iOS, Android, macOS, and Windows.
The free plan of Hotspot Shield offers 500MB of data limit each day. This sums up to 15GB of data each month.
As for downsides, the free version of Hotspot Shield is full of annoying advertisements. You can upgrade to the premium plan to get access to unlimited bandwidth coupled with the ability to connect five devices simultaneously.
Best Paid VPN Services For 2020
1. ExpressVPN
The first and possibly the most famous paid VPN service on the list is ExpressVPN. This mainstream VPN service is available for Windows, Mac, Linux, iOS, Android, BlackBerry and you can even use it on a router.
As expected from a paid VPN service, ExpressVPN offers unlimited bandwidth and users can choose 160 locations spread across 94 countries.
As for security, ExpressVPN offers 256-bit AES, DNS/IPv6 leak protection, kill switch, and split tunneling.
Overall, ExpressVPN is a trustworthy VPN service and even if you run into any trouble then the 24/7 email and live chat support is there to help you.
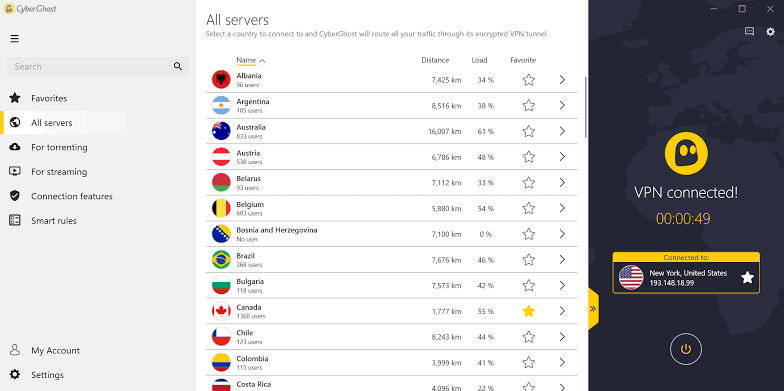
2. CyberGhost
The next best-paid VPN service on the list is CyberGhost. Similar to ExpressVPN, you can use CyberGhost on Windows, macOS, Linux, Android, iOS, and even on the fireTV stick.
CyberGhost has around 5921 servers which are spread across 89+ countries. Using CyberGhost you can easily access regionally locked content.
CyberGhost allows users to connect a maximum of seven devices simultaneously. Furthermore, this VPN service automatically blocks ads, trackers and malicious websites.
Lastly, CyberGhost uses military-grade encryption to safeguard your privacy.
3. NordVPN
NordVPN is another popular VPN service that offers 2048-bit encryption and allows users to secure up to 6 devices and that too with a single account.
In addition to smartphones and desktops, NordVPN also offers protection for smart TVs and routers.
NordVPN offers around 5,600 servers that are spread across 60+ countries. This top VPN 30-day money-back guarantee.
Consequently, if you didn’t like this VPN service you can easily get your money back. Lastly, NordVPN also offers 24/7 email and live chat support.
4. StrongVPN
The next best VPN provider on the list is StrongVPN. This private VPN hides your IP address and conceals your location.
Additionally, StrongVPN also claims that it never tracks, stores, or sells users data. Aforementioned unlimited bandwidth VPN ability to connect up to 12 of your devices concurrently.
In addition to the paid plan, StrongVPN also offers a free VPN plan. StrongVPN has around 950+ servers located around the world in 30+ countries.
Overall, StrongVPN is a trustworthy VPN service provider.
5. IPVanish
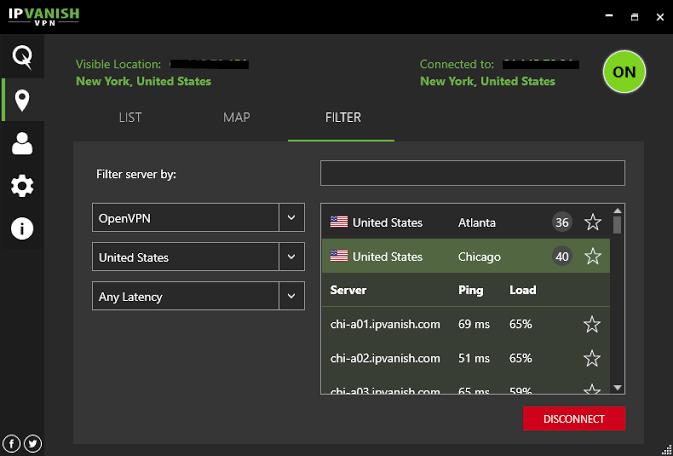
The last best-paid VPN service provider on the list is IPVanish. This unlimited bandwidth VPN is available for both smartphones and desktops. As for security, IPVanish uses 256-bit AES encryption.
You can effortlessly access censored apps & websites using IPVanish. Some of the major highlights of IPVanish are 40,000+ shared IPs, 1,300+ VPN servers spread across 70+ countries, unlimited P2P traffic, ten simultaneous connections, and 24/7 customer support.
How to setup a VPN?
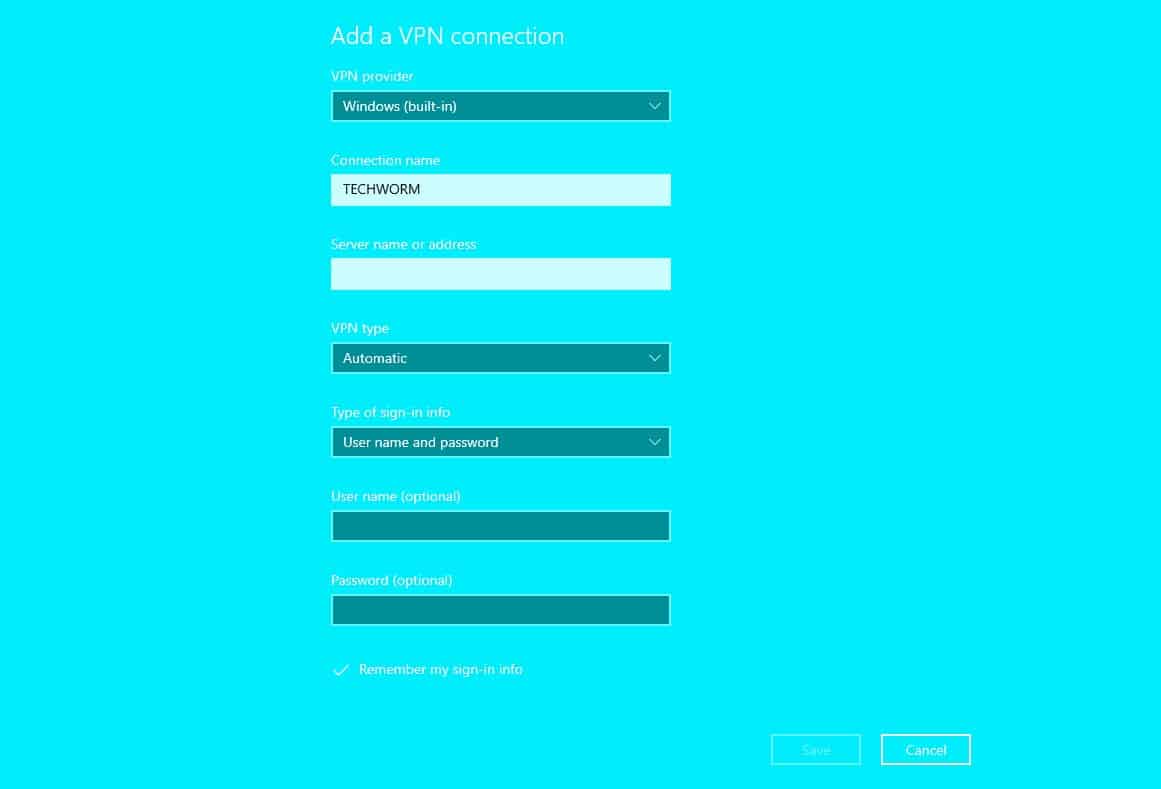
We hope that by now you must have selected a good VPN service. Well, now its time to set up and use this VPN service. To set up a VPN service on a Windows 10 computer follow these simple steps.
- Open Settings on your Windows 10 PC.
- In Settings, head-on to Network & Internet? VPN? Add a VPN connection.
- Lastly, click on Add a VPN connection and enter the details like Connection name, Server name or address, VPN Type, Type of sign-in info.
All these details will be provided by your VPN service provider.
Is a VPN Legal?
Yes, using a VPN to hide your IP address and access the Internet is a completely legal activity. That said, in certain countries Iran, Russia, China, and Turkey it’s illegal to use a VPN service.
If your country hasn’t banned VPNs then you can even use it to access location restricted content. As a result, you can even use a VPN for Netflix.
CONCLUSION
So these were some of the best VPN services that are worth checking out. Do share any of your personal recommendations in the comments section below.



You forgot to mention another PAID VPN provider, that can be used on unlimited devices
Surfshark
https://surfshark.com
Hey,You forgot to add PureVPN’s Christmas Deal that is 88% off on 5 year plan for the cost of $1.32/Month or $79 in full.
Hi, with this VPN can you download movies with. And how much is it a month.
I am glad to be a visitant of this utter website! , appreciate it for this rare information! .
My friend recommended a free solution—Atlas VPN for streaming netflix on my iPhone. They currently offer a free 3-month premium plan which is just how long I am expecting to be out of the states. Could you consider covering them in on of your reviews anytime in the future?