Curtailing Expenses Through Expedited Response
A Veritable Cybercrime Minefield
Cybercrime is pernicious, egregious, expensive, impossible to stop, and expanding. It’s like the digital flu. There is no cure, and it’s impossible to avoid entirely—but you can take protection measures which can keep such instances of infection from killing the body of your business.
Like the flu, those businesses most at risk for cybercrime are those that are burgeoning and those that are in decline. An older business that has been around near a hundred years and may not have all systems properly updated with modern security measures is like a senior citizen whose immune system has declined. A new startup is like an equally undefended newborn.
The middle segment, larger businesses which have reached their “cruising altitude”, are like adults who have properly developed immune systems. Such businesses have the resources to protect themselves against cyber criminals. They can even afford to be somewhat proactive in their response, chasing down criminals that may successfully extort them.
But there are many types of cybercrime, and it wouldn’t be characterized as a multi-billion dollar “growth” industry if such hackers didn’t regularly get away with substantial quantities of money.
Some kinds of cyber crime include phishing, adware, spyware, and ransomware. There are many others, but these are the primary cybercrime “mines” you’re going to encounter on the business battlefield. You need a proper security measure acting as minesweeper, or your business’s outbound profitability troops will suffer injuries, some of them terminal.
Internal Or External?
You can source internal security solutions, and to some degree, these will be effective. But cybercrime protection software and virus detection programs can only take it so far. After all, many cybercriminals are like those who install home security systems: they’re involved in future thefts.
A home security system installer knows which neighborhoods have the most assets, how to break into all their systems, and how to get out unscathed. Likewise, sometimes antivirus designers turncoat and become hackers, having a ready plethora of assets into which they can dip at a moment’s notice.
You could have an on-site backup system or several hard drives that you keep secure regularly; but unless you’re proactive in this method on a level that gets multiple versions of your files securely backed-up on a daily basis, you’re likewise in a prime position to lose assets through a hack attack.
The best solution is a proactive security service who backs up data to the cloud. Such services detect when there has been some digital incursion into your informational property, and then directly go after those entities responsible for the hacking.
According to CBISecurity.com, one of the best providers of information security services Detroit can offer, it is important for such tech solutions to “respond when you’ve been attacked.” This means your files are backed up as securely as possible, and every measure is taken to dispel an attack before a complete system reboot becomes necessary.
When you consider that 43% of hack attacks take place against small businesses and that 52% of small businesses are subject to being the target of cyber crime, the imperative nature of simultaneously proactive and reactive security solutions sourced through the cloud becomes nothing but evident.
Avoiding Likely Damages
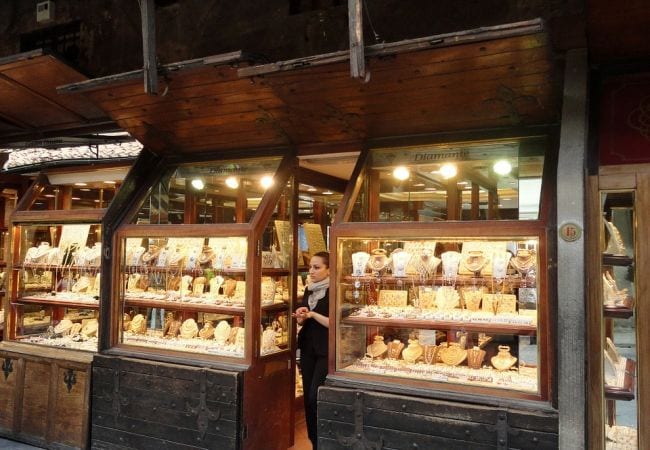
If your business has yet to introduce security protections against cybercrime, you’re a jewelry shop in downtown Compton who hasn’t put a lock on the door or any bars on the windows. The coming break-in is just a matter of time.
Even if you keep the jewels in a vault off the business premises, you’ll still have to fix the broken windows or the forced lock. I.E., even if you do self-sourced security solutions for your data, your systems still may bear the damage from external attacks. Professional digital security solutions are to be recommended for many reasons.