The Ultimate List of SD-WAN Benefits
SD-WAN has shifted from peripheral technology to the mainstream. SD-WAN benefits are so compelling that Gartner predicts that by 2018, more than 40% of WAN edge infrastructure refresh initiatives will be based on SD-WAN appliances from SD-WAN vendors or vCPE versus traditional routers (up from less than 2% today). According to IDC’s Worldwide SD-WAN Forecast, SD-WAN vendors are expected to see a 69% compound annual growth rate in sales over the next five years, reaching $8.05 billion in 2021.
“SD-WAN is the most significant infrastructure transformation since the introduction of virtualization,” says Shlomo Kramer, co-founder, and CEO of Cato Networks, a provider of cloud-based and secure global SD-WAN. “It transforms how we think about office-to-office communications, Internet access, the cloud, our security architecture, and mobility. When else have we seen a technology with such profound impact?”
Clearly, plenty of people are getting excited about SD-WAN benefits. There are also plenty of reasons already discussed for that excitement. Here’s my “ultimate” list of SD-WAN benefits, including a few you probably haven’t considered.
Align Your Business and Your WAN
For too long, our networks haven’t reflected our business priorities. Business-critical applications were starved for bandwidth while YouTube and, worse, BItTorrent, got treated like royalty. Sales calls were garbled while file transfers chugged along. SD-WAN allows us to make order of this WAN “mess” and align our backbones to our business priorities.
This means more than just allocating bandwidth by the application’s importance to the business. Even with traditional wide area networks, we’ve been able to do that with the right edge equipment. With the SD-WAN, we can also align the uptime and network performance characteristics of available data services to the importance of a site.
Business-critical locations, such as a datacenter, can be connected by active/active, dual-homed fiber connections, managed and monitored 24×7 by an external provider. Less critical locations, such as small offices, can be connected with a single xDSL connection for significant cost savings. Temporary teams, such as those put together for disaster situations or when onboarding new clients, can be set up with 4G/LTE and mobile clients for connecting into the SD-WAN. Yet despite their different forms of connectivity, all locations remain governed by a common set of routing and security policies.
By aligning the WAN’s usage, configuration, and availability characteristics to business needs, we’re able to maximize our WAN budgets and dramatically improve our return on investment (ROI) from SD-WANs.
Get Better Application Performance
Applications vary in their network requirements. Voice is sensitive to packet loss and jitter; bulk data transfer requires throughput. Web applications have their own needs. IP routing, particularly as it’s implemented on the Internet, doesn’t respect those differences – it selects the same optimum route for each application. As a result, some applications may starve while others thrive.
SD-WAN lets you be smarter about how you pick your routes. SD-WAN appliances monitor latency and loss metrics of the paths to all other SD-WAN appliances. Then, they match application requirements and business priority onto those metrics, selecting the optimum path for a given application. The upshot: companies can reach peak performance across any provided transport.
Reduce WAN Opex and Capex
The benefits of Software-Defined Networking (SDN) may have not been easily realized in the datacenter, but they’ve been pretty apparent in the WAN. The ROI of an SD-WAN can be dramatic and immediate. Replace MPLS bandwidth with Internet bandwidth and save 70% on bandwidth costs.
Operational expenses also become much lower. With zero-touch provisioning, bringing up a new location can be done in minutes and without specialized expertise. Just plug the SD-WAN appliance into the network. It does the rest. If security is integrated into the SD-WAN, you can eliminate your security appliances and save on the upgrading, patching, and maintenance.
Junk Your MPLS Provider — For Good
Getting MPLS-free. It’s the dream of many WAN managers. The legacy technology has forced companies to pay a premium for bandwidth, suffer long implementation times, and wait for carrier bureaucracy to respond to change requests. Is it any wonder that Gartner found, after conducting over 3,500 WAN-related client inquiries and reviewing more than 500 service provider contracts in the past year, that “Enterprises are dissatisfied with large incumbent network service providers.”
SD-WAN unburdens companies from their service provider with the promise that they’ll be able to use the Internet to replace MPLS. The reality is that while some applications can shift to the Internet, many cannot. Loss-sensitive applications, for example, will underperform over time when traversing the Internet. The inconsistencies caused by Internet routing and congestion make it impossible to move those applications onto the Internet in any kind of predictable fashion. For those applications, organizations will still have retain MPLS or replace it with another SLA-backed backbone.
Run the WAN Without Engineering
For years, WAN has meant advanced engineering, mastering CLIs, and becoming fluent in arcane protocols like BGP and PBR. For many companies, managing their WANs this way is not scalable. Some lack the internal expertise, and others have the engineers but not the patience or tools to manage the many elements of their networks.
SD-WANs do not completely eliminate experience from running the WAN, but they do maximize engineering resource by making WAN deployment easier and simplifying WAN management. Policies drive configuration, which minimizes the configuration-drift between branch offices that complicates WAN support. Deployment policies are also important for zero-touch provisioning and deployment. Adding new application services across the WAN without adversely existing services becomes much easier.
Make Holistic SD-WAN Security a Reality
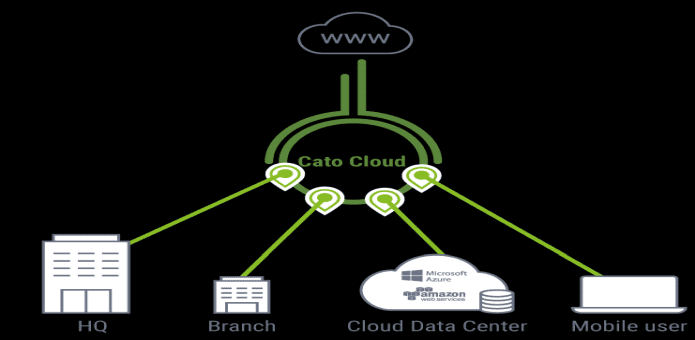
For too long, companies have thought about the security of their various resources in discrete compartments. Networking teams built the WAN and had their firewalls; mobile teams had their mobile VPNs. The cloud has given rise to its own security solutions. And all three had their own tools and policies. Companies ended up paying more operationally for this fragmented security infrastructure.
With the right SD-WAN, organizations can now create a holistic security posture that protects all of its resources. Mobile users, locations, and cloud resources can now connect into one network, the SD-WAN, which is protected by one holistic security policy with one set of security tools. It’s a radical transformation that makes security simpler and, by extension, more effective.
Protect Your WAN From Itself
Everyone assumes the WAN is secure, but that’s far from the truth. MPLS services send data in the clear but do nothing to prevent users from accessing unauthorized resources or the lateral movement of malware between locations. All SD-WANs address two of those problems. They encrypt traffic, preventing wiretapping. They also segment the WAN with layer three tunnels (called “segments” or “overlays”) that prevent users from seeing and accessing unauthorized resources in other overlays.
But most SD-WANs fail to do anything about the third category: Preventing lateral movement of malware within the organization. And make no mistake, preventing lateral movement is incredibly important. Just ask Target. The Target breach that exposed 40 million customer debit and credit card accounts, led to the resignation of senior executives, and was caused by malware moving between locations.
To stop lateral movement, the SD-WAN needs to be inherently secure, inspecting every packet between locations. This requires the delivery of next-generation firewall (NGFW), IPS, and advanced threat protection within the SD-WAN overlay. Some SD-WANs can deliver that kind of advanced security, while others cannot.
Better Uptime Makes for More Bedtime
Here’s the dirty little secret about MPLS services: the same errant backhoe operators that cut fiber cables and disconnect your Internet service are the same ones who crack your MPLS connections. What’s needed to make MPLS last miles secure are active/active, redundant, dual-homed, and diversely-routed connections.
But with MPLS, that hasn’t been possible for many reasons. Bandwidth costs have been too high for many companies to afford redundant connections. Even then, ensuring they were diversely routed has been impossible. Running two active connections can also introduce routing loops or complicate route configuration. Failover between them is also not fast enough to sustain a voice call or a session, for example.
SD-WANs solve the uptime problem. Their use of tunnelling make it simple to run active/active. The SD-WAN node load balances the connections, maximizing the available bandwidth. The traffic policies driving the SD-WAN determine the use of one path or another. Fast failover is an essential feature and one offered by many SD-WAN providers.
The WAN of All WANs
For too long, enterprise network teams have had to kludge together WANs and cloud services, routers and a security devices. The best next generation firewall, or the best security service in general, is one that’s built into the network – not bolted on top of one. Secure and optimized SD-WAN can replace the organically grown mashup of security and networking equipment with a sleeker, unified corporate network for all users, locations, and resources. Making them “intrinsically secure” renders the WAN even more agile, easier to configure, and powerful.
It’s enough to get any IT pro excited. Now, do you see why so many companies are intrigued by SD-WANs?
_____________________________________________________________________________________________________
Author Bio:
Dave Greenfield is the secure networking evangelist at Cato Networks. He brings more than 20 years of experience in IT and telecoms having worked as an award-winning journalist, blogger, and a technology analyst advising companies on their IT and WAN strategies. Dave is the author of the “Ultimate WAN RFP” and the “Essential Guide to Optical Networks.” He has a background in philosophy and computer science.