Many users are looking for an App or software out of parental controls, management needs and, of course, the issue of trusts between two partners. This kind of monitoring software can actually meet the needs of track the smartphones, but whatever you use it for, just keep it in mind, you must get approved before monitoring others’ devices due to the morality and privacy issues.
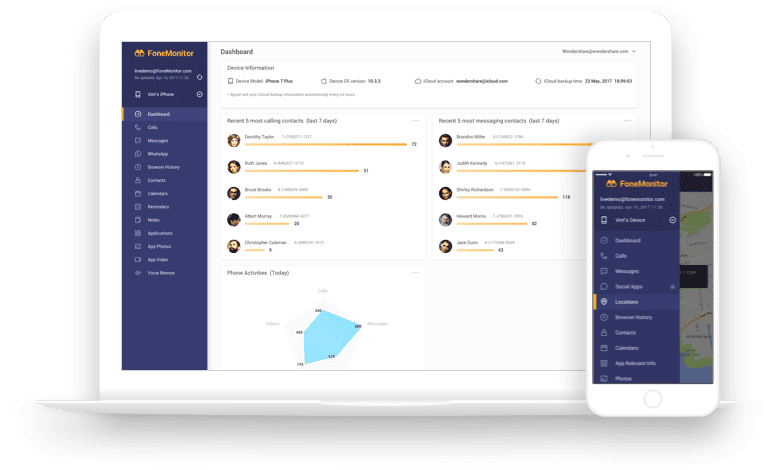
The software such as FoneMonitor that allows for monitoring any smartphone. Usually the users utilize it to monitor the targeted devices on their own smartphone or computer. There is no question about the legitimacy of this software, for example, with employees’ consent, it can be used to watch your staffs during the working period in terms of checking the text messages, Apps activity, keylogger on the targeted smartphones, to be sure if the workers are on duty or leaking out the confidential information.
Compatibility
FoneMonitor is compatible with both Android and iOS system, it allows for tracking the targeted devices on your smartphone as well as on the computers with Windows or Mac OS system, supporting all the popular web browsers, which include, Firefox Mozilla, Google Chrome, and Internet Explorer.
Installation (Easy steps to use FoneMonitor)
There are four simple steps you need to take in order to use FoneMonitor effectively:
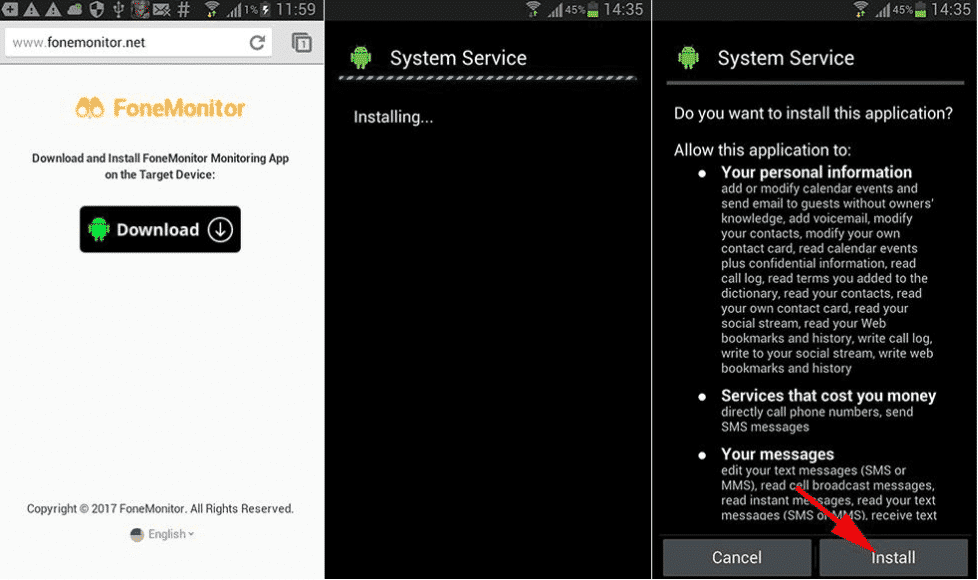
Step #1: download the FoneMonitor App on the Android devices from the designated page. On iPhone, it just requires to sync with iCloud, and you can start to use.
Step #2: Create your FoneMonitor account
Step #3: Verify the targeted smartphone
Step #4: Monitor the activities on the targeted phone.
For Android devices, you need to install the App on the targeted device, the App can be set to be invisible on the phone.
Features
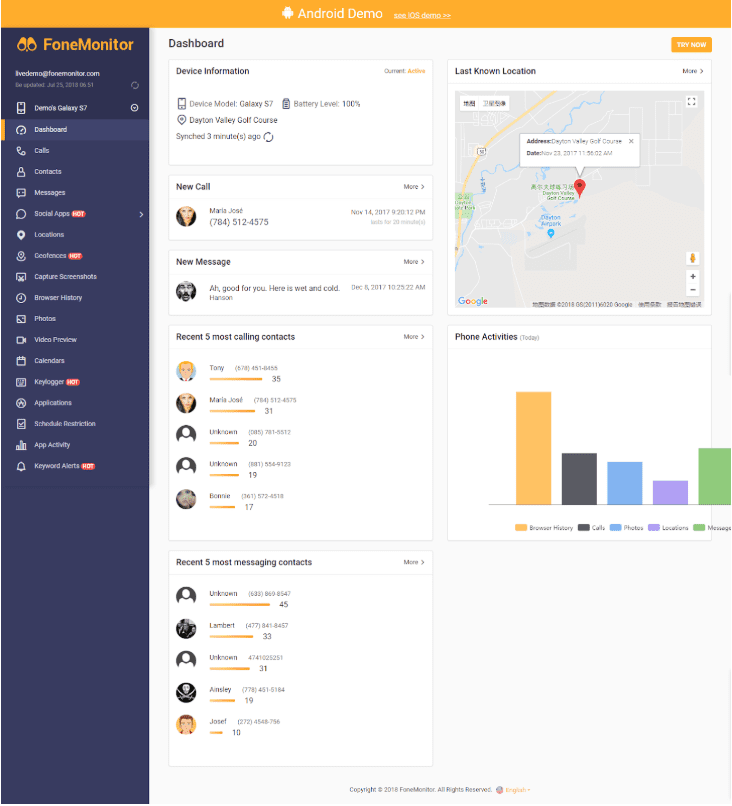
With FoneMonitor, you are able to monitor Calls, contacts, Social media Apps activity, instant messaging (including WhatsApp and Snapchat), downloaded applications, Browser history, Multimedia data, Notes, and Events.
- Ability to download and play any media attachments from the smartphone being monitored.
- GPS tracking to track the location of the device user.
- Provides information on user browser history- check all websites visited and the actions performed on each website and for how long the user has been visiting the websites.
- FoneMonitor keeps track of all photos shared, and received through Instant messages.
- It allows you to take screen shots of the messages and webpages of the device being monitored.
- FoneMonitor sends keyword alerts to your device, helping you to keep track of certain explicit words being used on the device you monitor.
- It features a “Schedule restriction” option. This feature allows you to create a time table for times you want to spy , it could be hourly or on specific dates.
- It comes with a video preview where you can actually watch a snippet of the video being watched from the device being monitored if you don’t have all the time to watch full videos.
- Social apps integration – This gives you one-time access to all popular social network being used by the device you are monitoring.
- Comes with a calendar feature that helps you schedule specific dates to monitor a device remotely.
- Applications- all the programs and applications being used on the monitored device will be revealed with the pressing of a tab.
- Geofences capability- This is a location-based service that relies on Wi-Fi to trigger a pre-programmed action even when the device being monitored has created a boundary.
- Keylogger capability- This feature will record all the key strokes used by the owner of device being monitored. This will help you gain access or have an idea of the words and sentence being typed by the owner of monitored devices.
- App activity monitoring- This feature allows you to track down the apps being used at specific period of the day and the actions taken on such apps.
In conclusion, the FoneMonitor app is a one-stop tracking solution with endless possibilities. It tracks one device at a time but all connections with the device can also be monitored with the purpose of unravelling the identities involved.