Table Of Contents
Ever since the networking has made its debut in the technical world,”hacker” has been a thrilling and fascinating concept. A hacker is someone who loves to discover new shortcuts of doing things to minimize the invested time.
In context of cyber world a hacker is someone who breaches the components of networking system. A hacker may be a Black Hat(does Hacking with malicious intends without asking the corresponding authorities), a Gray Hat(does it without asking the authorities but is not ill-intended) and a White Hat(does it only after getting the permission in writing and after being asked to do so by the corresponding admins).
There has been a large number of talent-packed hackers who are equipped with high level technology and knowledge that can do damage beyond someone’s thoughts. Here is a list of such hackers and hacking groups:
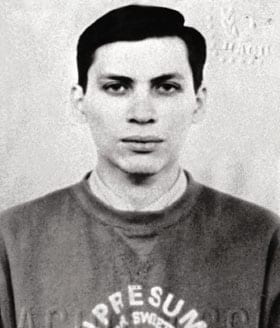
1.Adrian Lamo:
Adrian Lamo was known as the “homeless hacker” for his transient lifestyle. Despite that, he was able to hack into the internal computers of The New York Times in 2002.
This hack gave Lamo access to private databases, including one that had the private information of more than 3,000 people who had contributed to the paper’s Op-Ed section. He was sentenced to two years of probation and fined nearly $65,000. Most recently, Lamo was back in the news for turning in Chelsea Manning for leaking classified US Army documents.
2.Vladimir Levin:
This Russian hacker became famous in 1995 when he, without using Internet, hacked CitiBank’s computers and stole nearly $10 million from various global accounts. He just cracked the telecommunication system of the bank to listen customers sharing their personal account credentials.
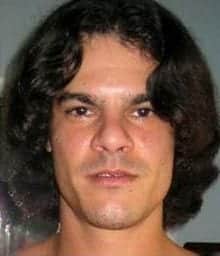
3.Albert Gonzalez:
He executed one of the biggest identity thefts in the history of Cyber-crimes. He was sentenced to 20 years in prison after his confession of stealing details of millions of debit and credit Cards. According to Associate Press, he was accused of stealing 170 million credit card numbers.
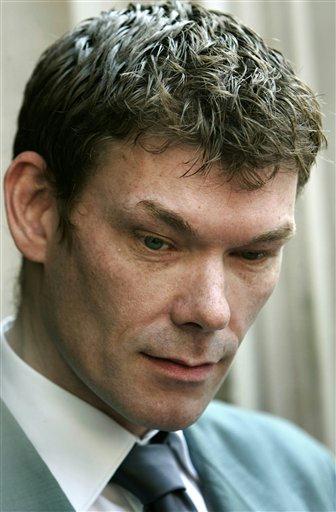
4.Gary McKinnon:
He was all over the news when he gained access to 97 American Military Networks between 2001 to 2002 and then left a message on their website “Your Security is Crap”.
A computer prodigy by the age of 14, McKinnon was known for his preternatural way of infiltrating closely guarded computer networks. What’s of note about McKinnon (beyond his insanely-good hacking abilities) is that he was on a quest to prove the existence of UFOs.
In fact, McKinnon claims that he was able to access images of potential alien spacecrafts during his hacks, although his connection was too slow to actually download the photographs. The US has tried to extradite him, but he has taken assylum in United Kingdom.
5.Kevin Poulsen:
Kevin Poulsen was known as Dark Dante, a young 20-something hacker with a penchant for mischief. His alleged exploits include hacking into the LA phone networks to ensure he won a prize from a radio show and even hacking into the phone calls of a “Hollywood starlet,” according to The New York Times.
After the feds started looking of him, Poulsen went on the run for 17 months. He was featured on the popular TV show “Unsolved Mysteries.”
In what is considered one of the most famous hacks, when the show displayed a phone number for viewers to call-in they had any information, the phone lines for the program went instantly dead. After serving time for his online crimes, Poulsen turned to journalism. He now serves as a contributing editor at Wired.
6.The Syrian Electronic Army:
After beginning as a rogue inline group in 2011 to support Syrian President Bashar al-Assad,it became a hacking group that used to create havoc by launching DDoS attacks on famous websites. The group is still active and is one of the most well known hacking groups of today. They generally target Western organizations including media outlets, who oppose Syria.
7.Max Ray “Iceman” Butler:
Max Ray Butler who had the alias “Iceman” was a computer security consultant before converting to one of the biggest hackers of all times. Arrested in 2007, Iceman digitally stole 2 million credit card numbers and ran up over $86 million in fraudulent charges. The federal authorities accused him of operating an online forum known as “Carders Market,” where hackers bought and sold stolen financial data. Butler is serving a 13-year sentence, which was the longest punishment ever inflicted on a hacker at the time.
8.Astra:
Astra is the pseudonym of a Greek hacker who infiltrated the computers of the French aviation company Dassault Group and stole weapons technology data for over five years.
The information he accessed included confidential data about jet fighters and other military-grade aircrafts. Astra then sold this secret information to numerous countries over a span of five years. As a result of this infamous hack, Dassault’s losses hit more than $360 million. The actual identity of Astra has never been revealed, but when he was apprehended in 2008 the authorities described him as a 58-year-old mathematician.
9.Anonymous:
Anonymous is the name of the decentralized hacktivist group well known for carrying out online hacking campaigns in support of some political or social events. Their icon is Guy Fawkes Mask. The group began in 2003 in the online forum 4chan. It first began as a way for online members to collectively pull pranks, but it morphed into an online “vigilante” service seeking justice on the Internet. The group has targeted the Church of Scientology, the KKK, Paypal, and many other high-profile institutions. It is known for its tagline, “We are Anonymous. We are Legion. We do not forgive. We do not forget. Expect us.”
10.Kevin Mitnick:
One of the best hackers to date. During his childhood he used to make free calls by his hacked mobile phone and stole secret codes from companies including Sun Microsystems and Novell as reported by New York Times. He even admits of hacking into phone calls of NSA(National Security Agency), according to The Times. After facing charge of being guilty to multiple cases of fraud in 1995 and serving several years into prison,he now works as a security consultant.
The World is still full of dangerous hackers, some are hidden and some operate in open. The above list is just a chunk of the show.