Table Of Contents
Telegram cross-platform messaging flaws allow hackers to bypass encryption and access user messages
Apparently the Secret Chat feature of Telegram saves messages in plain text in the memory dump
Is Telegram secure? not any more! Telegram cross-platform messaging App which was hailed as the most secure messaging App by Electronic Frontier Foundation, has been found to be not so secure after all.
Researchers from security firm Zimperium have discovered that Telegram can be hacked by cyber criminals in two ways. Zimperium’s founder and CTO stated on Zimperium blog that after conducting research on Telegram App, the researcher have found that there are at least two methods that can be leveraged to bypass encryption and obtain messages.
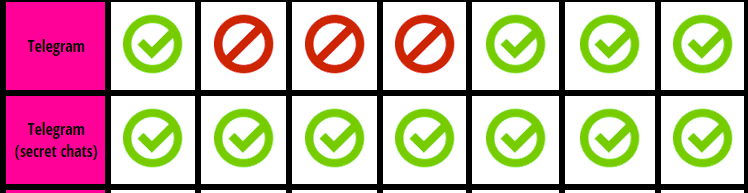
Telegram has around 55 million active users around the world and has a Secret Chat feature for a one on one private and secure chat between two users. Secret Chat works by giving encryption and decryption keys to the receiver and sender, thus making it most secure. EFF in its December secure messaging Apps audit and review had given maximum score to the Telegram’s Secret Chat feature.
According the Avraham, Telegram is vulnerable to the potential hacker gaining complete control of the targeted Android smartphone installed with Telegram App, by leveraging a kernel exploit to elevate privileges. Once the attacker is in control of the smartphone, he can dump process memory and gain access to any file stored on the device.
Zimperium researchers noticed that Telegram Secret Chat messages are stored in the Telegram memory dump in plain text and easily accessible to the hackers.
The researchers further discovered that a database file (Cache4.db) containing tables that store the secret messages is also in plain text. While Telegram users can delete their messages using a special function, the deleted messages can still be retrieved from the process memory, Avraham stated.
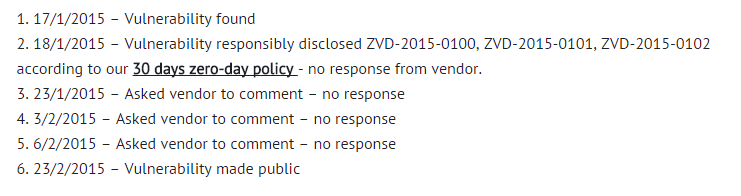
“While Telegram was founded upon a noble goal of providing privacy to consumers everywhere at no cost, they have fallen short of their objective by focusing purely on data-in-transit versus protecting data-at-rest on the mobile device itself. What is regrettable is that I approached Telegram multiple times and have yet to receive a response,” Avraham explained in a blog post. “Telegram’s so-called powerful encryption is not protecting users any better than any other page or app that uses SSL. If you are using Telegram because you want to ensure your privacy and the privacy of the messages you are sending, be aware that it will not stop sophisticated hackers from reading your messages. We highly recommended adding additional protection to your mobile device that can detect device-level cyberattacks.”
Avraham said Zimperium made the vulnerability public after the expiry of 30 day disclosure guidelines and in the absence of any reply from Telegram about the flaw. Telegram is yet to come out with a statement about the flaw.