14,000 decryptor Keys For CoinVault, Bitcryptor Ransomware Released By Kaspersky for ransomware victims
Kaspersky Lab announced the end of the ransomware variants, CoinVault and Bitcryptor by releasing over 14,000 decryptor keys required to unlock files encrypted by these variants, thereby, giving chance to the victims to get their files back for free.
Ransomware is a particularly virulent type of malicious code which spreads through downloads, phishing campaigns and malicious links. Once a system has been infected, a lock screen appears and all files on the device are encrypted.
The cyber-security firm first discovered the CoinVault attacks in May 2014. Since then, this aggressive ransomware that heavily encrypts data files on infected computers and demands payment in Bitcoin for the encryption keys has made over 1,500 victims in more than 108 countries. The countries that have been hit hard due to the malware attacks include The Netherlands, Germany, the United States, France, and the United Kingdom. The ransomware has also characteristically offered victims a “free decrypt” to explain how the CoinVault’s authors could indeed unlock the encrypted files.
The CoinVault file-encrypting ransomware program was first documented by Kaspersky researchers in November 2014. Then, in April the National High Tech Crime Unit (NHTCU) of the Dutch police recovered some decryption keys from a seized CoinVault server.
After that raid, the program’s authors took a break, as the CoinVault malware campaign proceeded largely undeterred. However, they eventually launched a new version called Bitcryptor, a second-generation version of CoinVault. But, in September this year, the NHTCU suffered a blow when the Dutch law enforcement arrested an 18-year-old and a 22-year-old in connection to the ransomware attacks.
After police had gained access to the cyber-crooks’ infrastructure, Kaspersky Lab experts were able to extract all the remaining CoinVault and Bitcryptor decryption keys from the CoinVault’s command-and-control (C&C) servers that among other things had decryption keys, Installation Vectors (IVs) and private Bitcoin wallets, and publish them on the noransom.kaspersky.com website.
To study CoinVault further, Kaspersky researchers used these resources, and an analysis disclosed that ransomware uses the CFB block cipher mode as well as 256-bit AES among other things.
These findings enabled the security firm to upload a set of around 750 keys in its ransomware decryptor service in April of this year that were recovered from servers hosted in the Netherlands. Now, all 14,000 decryption keys are available through Kaspersky’s ransomware tool.
A coalition of security companies that investigated one of the most prevalent ransomware programs, CryptoWall 3.0, has made its authors approximately $325 million through extorting victims. Researchers say at least 400,000 infection attempts have been made across 49 CryptoWall 3.0 campaigns.
These findings enabled the security firm to publish more than 700 decryption keys in April of this year. Now Kaspersky has released all 14,000 keys.
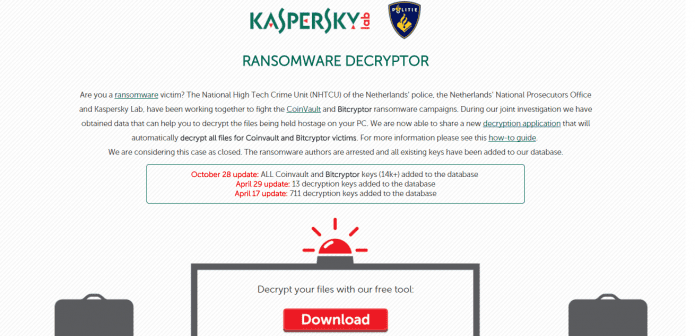
“The National High Tech Crime Unit (NHTCU) of the Netherlands’ police, the Netherlands’ National Prosecutors Office and Kaspersky Lab, have been working together to fight the CoinVault and Bitcryptor ransomware campaigns,” a page which hosts Kaspersky’s decryption tool reads. “During our joint investigation we have obtained data that can help you to decrypt the files being held hostage on your PC. We are now able to share a new decryption application that will automatically decrypt all files for Coinvault and Bitcryptor victims. For more information please see this how-to guide. We are considering this case as closed. The ransomware authors are arrested and all existing keys have been added to our database.”
Users who believe they have been affected by CoinVault can access the decryption key directly here.