A recent Unclassified Document from FBI, Shows How Android is being targeted for Malware attacks.
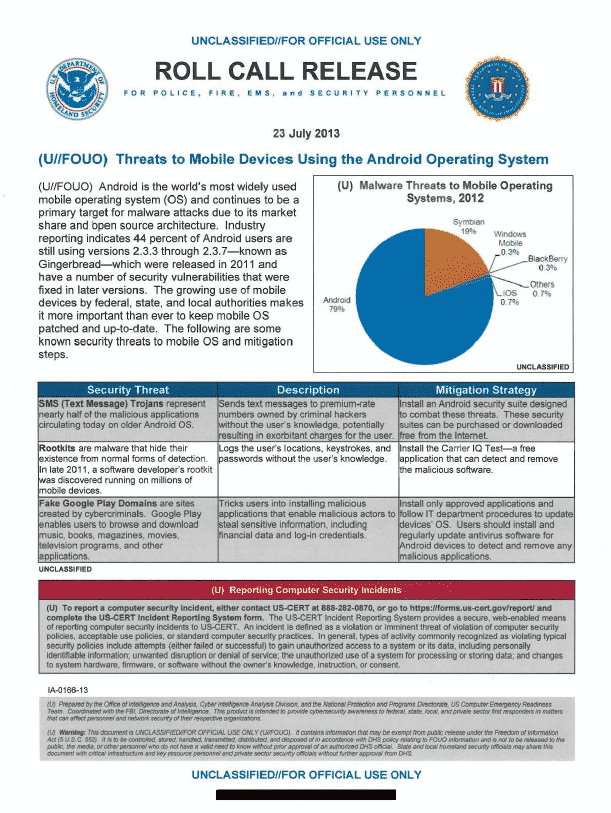
Android is one of the world’s most used mobile operating system, and has been targeted by Malware attacks due to its market share and open source Architecture. An industry reports states that more than 44% of Android users are still using the older version 2.3.3 of Android, released in 2011 which has number of known vulnerabilities, which have been fixed in later versions.
The document from FBI, was released for Federal, State And Local Authorities, warning them to keep their mobile phones patched and updated.
The document also describes 3 of the Major Security threats given below:
| Security Threat | Description | Mitigation Strategy |
| SMS (Text Message) Trojans represent nearly half of the malicious applications circulating today on older Android OS. | Sends text messages to premium-rate numbers owned by criminal hackers without the user’s knowledge, potentially resulting in exorbitant charges for tile user. | Install an Android security suite designed to combat these threats. These security suites can be purchased or downloaded free from the Internet. |
Rootkits are malware that hide their existence from normal forms of detection. In late 2011, a software developer’s rootkit was discovered running on millions of mobile devices. |
Logs the user’s locations, keystrokes, and passwords without the user’s knowledge. | Install the Carrier IQ Test–a free application that can detect and remove he malicious software. |
Fake Google Play Domains are sites created by cybercriminals. Google Play enables users to browse and download music, books, magazines, movies, television programs, and other applications. |
Tricks users into installing malicious applications that enable malicious actors to steal sensitive information, including financial data and log-in credentials. | Install only approved applications and follow IT department procedures to update devices’ OS. Users should install and regularly update antivirus software for android devices to detect and remove any malicious applications. |