Samsung lets you hack it smartphone even with factory reset protection enabled with a USB OTG
In order to protect a Android smartphones from theives, Google introduced a new feature in Android 5.0 Lollipop. The new feature allows your phone to stay protected in the event of a factory data reset that occurs from within recovery. Android 5.0 Lollipop gives this root level protection to Android smartphone owners and it will persistently ask for the primary Google account’s password after a phone has been factory reset in this manner. This protection helps the owner in case a thief or a hacker tries to gain access to the phone.
However, a Android user, RootJunky has proved that it is easy to bypass this system level protection with just a USB OTG cable and APK within 10 minutes. RootJunky recently discovered a flaw on Samsung devices which allows you to bypass the system level protection with just that.
In a new video, RootJunky demonstrates how in just 10 minutes he was able to navigate around Factory Reset Protection in a Galaxy Note 5. This security feature is meant to make it impossible for someone to take your phone and just perform a factory reset as a way to make it their own.
Due to the flaw in Samsung devices, when you attempt to insert an OTG drive into an Samsung Android smartphone, the OS allows you to open files on it, even when you should be locked into the screen requiring a Google sign-in after the factory reset. He put an APK on the OTG drive that does nothing but open up the settings. From there, just install the APK—yes, the OS even lets you disable the “unknown sources” security measure in this state—and you will be given free reign over the settings.
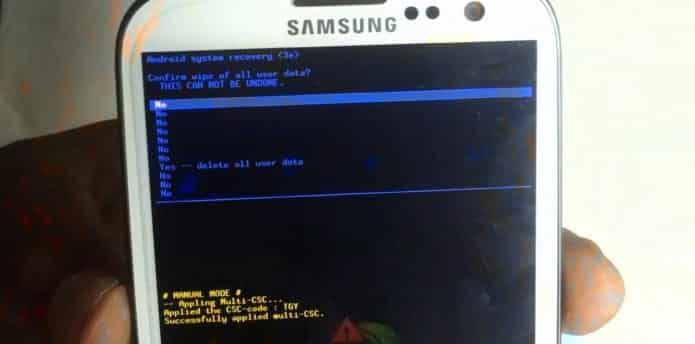
To finally bypass the reset protection, you just factory reset from the settings rather than from recovery. After that, the phone will be a clean slate.
With this method, thieves and hackers could could steal the costliest Samsung smartphones like Galaxy Note 5, Samsung Galaxy S6 and S6 Edge and sell them as new to unsuspecting buyers.