Smartwatches and other wearable devices can be used as motion-based keyloggers to spy on you
Tony Beltramelli, a computer science Masters student and software engineer, in his graduate research work at IT University of Copenhagen “Deep-Spying: Spying using Smartwatch and Deep Learning” has presented a new attack method that allows to eavesdrop on passwords the user enters on his/her tablet screen, smartphone, PC keyboard, ATM machine, keypad-equipped safe or door from motion sensors in wearable devices.
“By their very nature of being wearable, these devices, however, provide a new pervasive attack surface threatening users privacy, among others,” Beltramelli wrote in the paper’s abstract.
“The goal of this work is to raise awareness about the potential risks related to motion sensors built-in wearable devices and to demonstrate abuse opportunities leveraged by advanced neural network architectures.”
In September 2015, a group of students lead by Romit Roy Choudhury, Associate Professor at ECE Illinois had developed a mobile app that analysed the movements of a smartwatch (a Samsung Gear Live smartwatch) to detect the keys pressed by the user.
Beltramelli’s research is an expansion on this previous work done by the group. In his research, he lessened the area of attack surface to 12-keys keypads, usually found on ATMs and the touch display of your smartphone, when using a PIN lock.
Using an RNN-LSTM (Recurrent Neural Network – Long Short-Term Memory) deep learning algorithm, he trained an artificial neural network that converts outputs of a wearable device’s gyroscope and accelerometer into a series of key strokes and is capable of keeping track and recognizing sequences of motions over time.
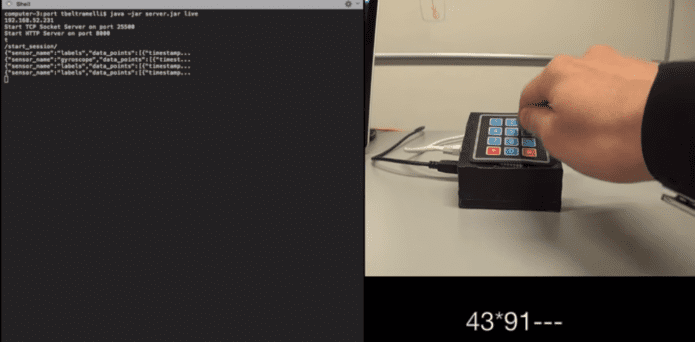
The software developed by Beltramelli collects motion data from a Sony SmartWatch 3, which he used to record accelerometer and gyroscope sensor data.
However, he was not able to send the data directly to a server due to the watch’s technical limitations, but he could send it to a closeby Android device (LG Nexus 4) (via Bluetooth), which then transmitted it to a server for further study.
He was able to sieve through all the data using an algorithm that combined Java, Python, and Lua code, and remove noise movements, and detect patterns for various events, like when the user enters a PIN code on an ATM’s keypad, or when the user moves and taps his finger on a phone’s touchscreen to unlock a PIN-protected phone.
“This architecture can achieve touchlogging and keylogging with a maximum accuracy of 73% and 59%, respectively,” Beltramelli explained.
“Moreover, the system is still able to infer keystrokes with an accuracy of 19% when trained and evaluated with datasets recorded from different keypads,” he also added. “This result suggests that an attacker could log keys from a wide range of devices even if its classifier is trained with measurements from a different compromised device.”
Everything is theoretical as of now, but he has also made the app and server-side code available on GitHub to advance his work.
To minimize the risk of such “touchlogging” and “keylogging” attacks, the author suggests that you wear your smartwatch or fitness tracker on the less-preferred hand – meaning if you are right handed, wear the device on your left hand and vice versa. Further, you also should be need to be careful about applications you install on your wearable device. In addition, it might be prudent to consider purchasing your next wearable only from a trusted manufacturer and via a trusted seller.