Researchers discover a way to crash Chrome and Firefox browsers on Linux PCs and Android smartphones
Imagine you are searching for a keyword on Google search using Chrome browser on your Android smartphone. The Chrome browser will immediately return the most plausible suggestions matching your search. Click on one of these search suggestions and suddenly you will find your Chrome browser has crashed.
This is due to a bug found out by security researchers from Nightwatch Cybersecurity. The researchers discovered that they can manipulate the search suggestions in a way to send big files to the browser and crash it. Their method relies on using the search suggestions feature that these browsers support. The researchers noted that the issue is not a software bug, but a design implementation that allows their attack to be executed.
Almost all of the current browsers have a search field or allow users to search via the URL address bar. Based on the search engines supported inside the browser, search suggestions can be shown as the user types their query. Nightwatch security researchers say that if the browser’s search engine provider doesn’t protect these search suggestions via an encrypted HTTPS channel, an attacker on the local network can intercept search suggestions queries and answer before the search provider.
PoC
Because browsers include multiple non-HTTPS search engines with insecure search suggestions endpoints, it would be possible for an attacker on the network level to intercept the traffic flowing between the browser and the search engine endpoints, and substitute their own. If a very large response is returned (2+ GBs), the browser can run out of memory and crash. This is due to the fact that browsers do not check for sizes in the search suggestions responses. Obviously, this is more of an issue for mobile devices which have lower memory than desktops.
For Android AOSP browser and Chromium, this issue appears to be directly tied to the processing code of search engine responses. For FireFox, this is a more generic issue around large XMLHTTPRequest responses, which is what the browser is using internally for search suggestions. Our bug reports with the vendors provide more details on which code is causing this. This re-enforces the fact network traffic SHOULD NEVER be trusted.
No malware
The researchers stated that though they could crash the browsers using the above method, they were unable to execute any malicious payload using this method. This means that the bug is more of a nuisance value than a threat.
Test results
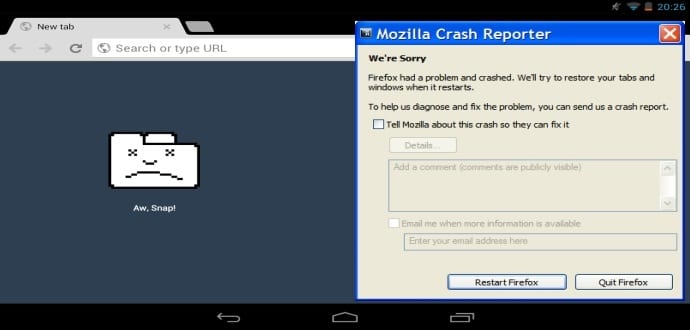
The researchers tested their PoC on various devices using Chrome and Firefox and the results are give below :
- Android AOSP stock browser on Android (v4.4) – application crashes
- Chrome v51 on Android (v6.01) – application crashes
- Chrome v51 on desktop Linux (Ubuntu v16.04) – the entire computer freezes requires a reboot (this maybe to due to swapping being disabled with an SSD drive)
- FireFox v47 on desktop Linux (Ubuntu v16.04) and Android (v6.01) – application crashes
The researchers found that their exploit doesn’t affect Apple’s Safari v9.1 browser or Microsoft’s Edge and Internet Explorer 11.
The bug can be exploited in the wild providing a potential hacker has the following at his/her service
- The attacker must have control over DNS and the network traffic of the victim machine. This is most likely in cases of a rogue WiFi hotspot or a hacked router.
- Most browsers have rather short timeout for search engine suggestions response, not allowing sufficient time for the large response packet to be transferred over network
- Due to the very large response size needed to trigger this issue, it is only exploitable over broadband or local networks such as rogue WiFi hotspot
The researchers informed the respective browser developers about the flaw. However, the Android, Chrome, and Firefox security teams declined to classify this bug as a security issue.