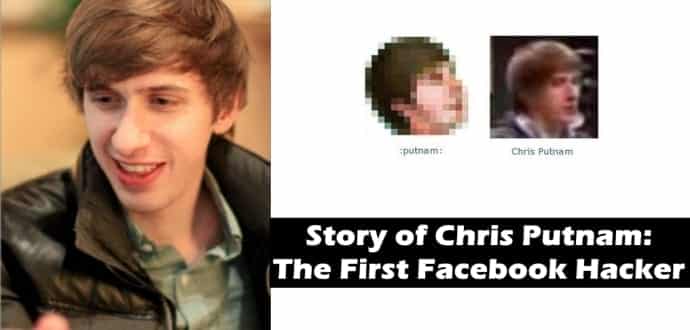
Chris Putnam : The First Facebook Hacker
If you’ve been a long time user of Facebook, you are sure to come across an emoticon of a man’s face facing upward to the right.
If you have asked your friends or googled how to do it, you know that all you need to type is :putnam: for the emoticon to show.
Have you wondered what putnam means ? Its not a word in the English language, so what could it signify ? That emoticon is the last name of a man named Chris Putnam and this is his story.
- :putnam: doesn’t works any longer to show up as an emoji
Hack Away
The short answer – the one you will most likely find on the internet – is that Chris Putnam is an engineer at Facebook. The full story however, is a little more entertaining. At the end of this article, you will also realize that it wasn’t Putnam who added his emoticon to Facebook chat, it was his friends that did it.
Around the end of 2005, Putnam carried out a series of pranks on Facebook alongside his friends Marcel Laverdet and Kyle Stoneman. One of these, was an XSS based worm that spread through Facbook profiles by means of an un-sanitized profile field.
Our worm code would rapidly and silently copy itself from profile to profile, spreading virally through friends viewing one another’s profiles. The code itself was run off of an off-site server under my control, so at any time I could change the script that was running on everyone’s profiles, says Putnam on his blog.
Before seeding the worm Putnam and Marcel had co-written a JS library that could replicate some of Facebook’s functionalities including adding a friend, poking, messaging, wall posts, among others. This allowed them to modify the master script to carry out actions through the infected accounts. The first version of this worm would include this library and would also send a friend request to his test account thus, allowing him to easily track the number of infected users as the outstanding friend request number ticked up on his homepage.
During this time, his friends were working on a CSS stylesheet that would re-style a Facebook profile to look like a Myspace account ( as it looked in 2005). It would modify every single field on the profile and make it look exactly like a Myspace account including the colour scheme. Thus the first version of this worm would do 3 things
- It friended his test account
- It re-styled the profile to look like MySpace
- It copied itself to your own profile.
Facebook gets Involved
The modified profiles however, would barely last a day before the user complained to Facebook about the problem. This also led to a number of Facebook employees having their accounts infected including internal test accounts known simply as ” The Creator ” leading them to infer that they might have possibly infected the account of the Facebook founder ( since he was technically the creator ).
He states, that in hindsight, he should have tried to spread the worm as much as he could without having the infected profile showing any changes but he was confident that the company would identify the XSS vector before they could’e had an opportunity to do anything with it. He says his friends are still annoyed at this fact. Putnam and friends didn’t stop there though, they released a second worm shortly thereafter that was controlled by Marcel and allowed him to post random messages to random friends’ walls (e.g., “Hey, nice shoes.” or “This wall is now about trains.”).
As fixes started rolling out for the worm, I got a message in my personal Facebook inbox from co-founder Dustin Moskovitz. His knowledge of my identity didn’t come as much of a surprise since the worm’s interaction with my account was a dead giveaway and we even went out of our way to provide contact information in the source code and CSS file. I’m having a hard time finding the exact text of his message right now, but it was along the lines of “Hey, this was funny but it looks like you are deleting contact information from users’ profiles when you go to replicate the worm again. That’s not so cool.”
This led to a string of messages being exchanged between him and Dustin where he explained the worm in details along with other loop holes that he had discovered. In the meantime, Putnam was looking to get a job and move to Silicon Valley. In 2006, about a year later, he managed to get a job interview from a company based in Silicon Valley through a friend. When he mentioned this to Dustin, he was called for an interview at Facebook.
“Now, this seemed pretty nice and all, but this was a period in tech history where MySpace had just gone through something extremely similar–guy makes harmless XSS worm, company offers to hire him–but in their case, they had him arrested as he arrived at LAX and turned him into a convicted felon.”
The Interview
With apprehensions in mind, he still went for the interview. He brought a friend along and stocked up on cash just in case things took a wrong turn. Until the moment when he entered Facebook’s offices and found Dustin waiting for him without cops, that he breathed a sigh of relief. The interview went off well and just a few days later, Putnam found himself employed at Facebook.
We end this piece with Putnam’s own words, ” I will be forever grateful that the company was so sympathetic toward people like myself. It’s one of the things that really sets Facebook apart with its passion for scrappy, hacker-type engineers”