The Malware ‘Win32/Qadars’ which operates almost similar to Zeus, since it is using some of its code is much more improved than Zeus or any other Banking trojan. Win32/Qadars uses various webinjects to hook selected API’s In Browsers including Internet explorer, Firefox or Android mobile components.
The injected component is usually a form asking for Victim’s phone number and mobile number, which then sends a sms link to victim to download a mobile application, while the complete process is going on, victim is shown a message saying, ‘that as more and more fraudsters manage to intercept the SMS authentication codes sent by banks to their clients, the bank has developed a smartphone application to prevent such interceptions’
Until the access code displayed by the mobile application is inseted, the injected code prevents the victim to access his account.
This mobile application which is of course a fraudent application is then used to steal banking information from mobile phones.
In addition to Fake form the Malware is also able to run javascript that can do automatic transactions from bank account without the victims Knowledge.
Once the Qadars is downloaded it looks for folder inside the %APPDATA% folder and chosses a random subfolder going upto the depth of maximum 4 directory and hide itself there with a randomly generated name of 7 Characters. which helps it to be well hidden and to ensure to be not found in routine checkup.
The author seems to be actively updating the code the first version 1.0.0.0 has been updated and the latest one is 1.0.2.7, which have increased the infection rate in recent days.
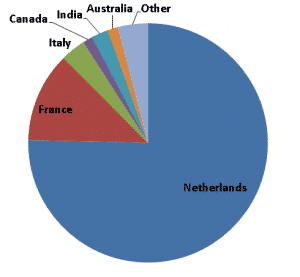
A recent report from eset shows the infection rate is highest in Netherlands followed By France, Italy, India, Australia and Canada.
The recent evolution of Banking Malwares have increased the infection rate and Fraudent cases. in Recent years various other banking malwares such as Win32/Napolar, Win32/Hesperbot, Win32/Zbot and Win32/Carberp, few of which can alos bypass two steps authentication of banks have caused a serious problem in the way of Banking security.