The Full-Disclosure List is being shut down from yesterday i.e 19.2.2014 after a successful run for 12 years.. This Full-Disclosure List was started by Len Rose and John Cartwright on 9 July 2002 and hosted and sponsored by Secunia. Hackers both ethical and blackhat ones, security enthusiasts and researchers loved this list while the corporates hated it. This may be the reason for John pulling down the list indefinitely.
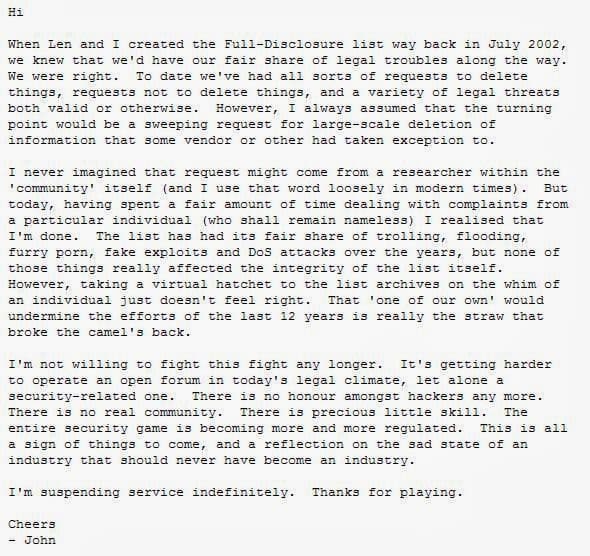
John Cartwright issued a text file announcing this decision and attributed it to the pressure being put on him by an unnamed security researcher, whom he calls ‘one of our own’ to remove large amounts of content from the list archives. Apparently after all the legal runins this was too much for both John and Len.
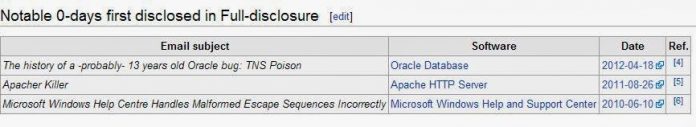
Both of them had launched the Full-Disclosure List back in 2002, with a single mission > to allow anonymous reports of security problems, not necessarily with prior disclosure to the maker of the product. This led to many a problems between the vendors and the duo as vendors generally prefer to find the security problems, zero day vulnerabilities and loop holes with the help the security researchers confidentially before the public announcement of the exploit. They prefer to announce the exploit and the patch simultaneously but F-D allowed hackers and researchers to post the vulnerabilities even before anybody from the company new it. This generally led to a cold war kind of situation between the Vendors and the authors.
The first post after the launch of Full-Disclosure was “IIS double UTF decoding bug (old) exploit: IIS explorer”. This was an old vulnerability, but the posting included a script kiddie-friendly PHP exploit.
Many have felt that Full-Disclosure in no longer useful in today’s Twitter and Facebook times. Most vulnerabilities, exploits and hacks are now generally Tweeted and it spreads from there. Tod Beardsley, Engineering Manager at Rapid7 stated, “…today, we have lots and lots of high-quality alternatives [to Full-Disclosure]. Heck, just have a Twitter or Google News keyword of “Metasploit”and you’ll get some pretty decent intel on what the world is looking at. Projects like OSVDB and Exploit-DB also very handily fill the role that F-D pioneered of ensuring that public access to vulnerabilities is still possible.”