Table Of Contents
Was the FBI tricked in ‘Operation Onymous’ Analysis casts doubt on FBI claims
In the week gone by, the FBI carried out Operation Onymous, which was targeted at taking down hidden websites in the dark web known for carrying out illegal activities. They apparently seized over a million in bitcoins, $180,000 in cash and drugs among other things. However several analysts have cast doubts over the authenticity of the websites seized in the operation.
Clones
“[We are] most interested in understanding how these services were located and if this indicates a security weakness in Tor hidden services that could be exploited by criminals or secret police repressing dissents,” the Tor group had said. They were left clueless as to how the FBI managed to track down these sites and even asked the public at large to locate any loopholes in their system. But if the new analysis are to be believed, privacy advocates may have little to nothing to worry about.
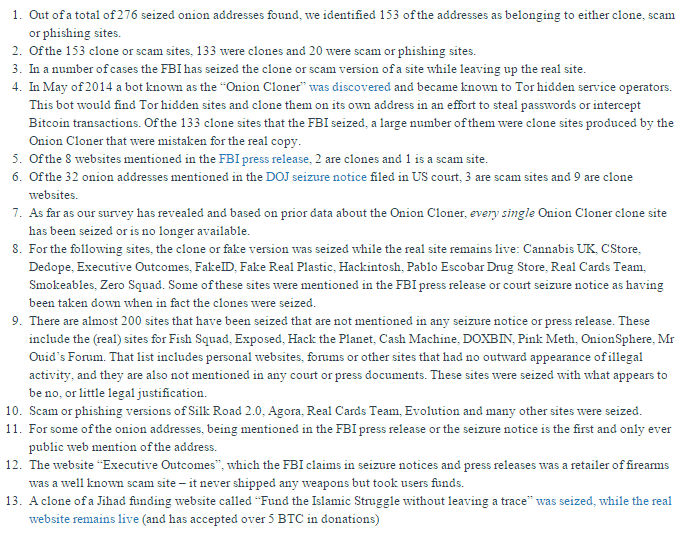
The new analysis published on Monday on Nikcub by Nik Cubrilovic reveals interesting findings that place the law enforcement agencies’ rather tall claims about the raids doubt. Blogger Nik Cubrilovic and others conducted a web crawl on the Tor network, and according to the Australia-based blogger, while Europol and the FBI claimed to have seized 410 services, a crawl of over 9,000 onion sites found that only 276 services were taken down. 153 of these websites were clones or phishing scams while 20 more were malicious websites.
“In May of 2014 a bot known as the ‘Onion Cloner’ was discovered and became known to Tor hidden service operators,” Cubrilovic writes. “This bot would find Tor hidden sites and clone them on its own address in an effort to steal passwords or intercept Bitcoin transactions. Of the 133 clone sites that the FBI seized, a large number of them were clone sites produced by the Onion Cloner that were mistaken for the real copy.” He also claims that a number of other sites, claimed to have been seized by the FBI have no mention in official documents.
Cubrilovic says:
That the FBI seized so many clone and fake websites suggests a broad, untargeted sweep of hidden services rather than a targeted campaign.
The slapshot nature of how sites were seized suggests that rather than starting with an onion address and then discovering the host server to seize, this campaign simply vacuumed up a large number of onion websites by targeting specific hosting companies.
This comes as very good news for people with privacy concerns. Though it is to be admitted that the anonymity of Tor is abused by many to carry out illegal activities, it also provides users with a cloak of anonymity in regions where it is a very dire asset and loopholes that allow authorities to track down users will have very far reaching impacts. In this case though, the FBI seems to have cast a huge net into the wild and managed to get lucky with lots of fishes. Taking out lots of criminals and at the same time maintaining the privacy bubble secure.