Table Of Contents
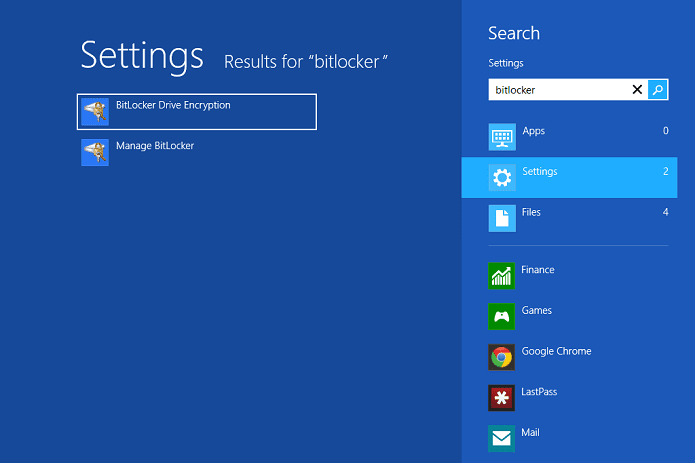
Microsoft’s Bitlocker for Windows is vulnerable to a simple bypass
It is time that you chose an alternate form of security to safeguard your Windows folders
If you have been using BitLocker to keep your files safe, then it is high time that you searched for a much more suitable and secure alternative because the disk encryption solution implemented in the Windows operating system can be bypassed with relative ease. According to a researcher, BitLocker does not need sophisticated tools or exploits to be bypassed. However, in order to bypass the encryption, the computer will need to have obsolete security patches running on it.
Security researcher Ian Haken claims that BitLocker is available on professional and enterprise versions of Windows. Additionally, the data encryption implementation was also designed to protect the pre-boot process from modification (the BIOS screen) through the use of a Trusted Platform Module, or TPM for short.
Ian Haken, who is currently stationed at security firm Synopsys was able to discover a vulnerability that could allow a potential attacker to bypass the authentication and to decrypt drives encrypted with BitLocker.
However, there are certain conditions that need to be satisfied for the exploit to be successful. BitLocker on the target system has to be enabled without a PIN or USB key and the system should be joined through a domain network. What is even more important to note here is that the attacker needs to be physically present there in order to complete the process since there is no way to complete this through the use and the attacker needs physical access to it.
In order to bypass authentication, Haken has explained the following:
“The attacker needs to set up a Kerberos Key Distribution Center (KDC), needs control of the network communication and needs to direct communication to the attacker-controlled “mock” domain controller. By connecting the machine to the mock domain controller (DC), the attacker can trigger a password reset action, thus gaining access to the encrypted drives.”
Haken has stated that this particular kind of attack has a 100 percent success rate on affected systems, does not require any sophisticated tools and can be completed in a matter of seconds. If such a thing is true, then it is high time that you looked for a suitable alternative.