Catalogue of smartphone spying equipments the Feds and police don’t want you see
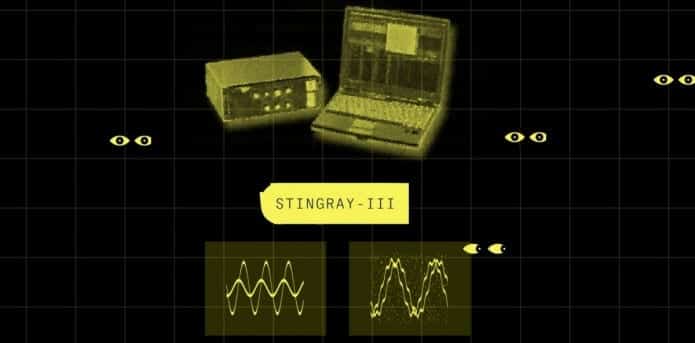
Want to know what kind of equipments the United States law enforcement agencies use to snoop on your cellphone? A secret internal U.S. government catalogue containing dozens of cellphone surveillance devices used by the military and by intelligence agencies have been obtained by The Intercept. The catalogue includes mostly variants on the Stingray/Dirtbox, which pretend to be cellular towers in order to gather the subscriber details of all the people within range (up to an entire city, for the airplane-mounted Dirtboxes).
“The Intercept obtained the catalog from a source within the intelligence community concerned about the militarization of domestic law enforcement,” states the post published on The Intercept.
“A few of the devices can house a “target list” of as many as 10,000 unique phone identifiers. Most can be used to geolocate people, but the documents indicate that some have more advanced capabilities, like eavesdropping on calls and spying on SMS messages. Two systems, apparently designed for use on captured phones, are touted as having the ability to extract media files, address books, and notes, and one can retrieve deleted text messages.”
Some are designed to be used at static locations, while others can be discreetly carried by an individual. Other have names like Artemis, Blackfin, Cyclone, Gilgamesh, Jugular, Maximus, Spartacus and Yellowstone.
The capabilities and costs of the different devices that are in use in at least 60 law enforcement agencies in the US are detailed in the catalog, though most of the law enforcement agencies will not admit to owning them. While some of these devices are paid for with civil forfeiture funds stolen from random citizens, they are more often bought with DHS anti-terror grants.
The catalog also includes 53 cellphone spying devices, including Stingray I/II surveillance boxes and Boeing “dirt boxes.”
Small enough to fit in a backpack, there are some devices such as the REBUS Ground Based Geo-Location that “provides limited capability to isolate targets utilizing Firewall option.”
The document also includes many other cellphone spying devices that are less popular than Stingray but could be used by law enforcement and intelligence agencies in various scenarios, including the deployment on drones and aircrafts.
Within the catalog, the NSA is listed as the vendor of one device, while another was developed for use by the CIA, and another was developed for a special forces requirement. About a third of over 50 devices described in the document are so secret, they had not been described in public before.
The cellphone spying devices have been used by local law enforcement agencies across the United States for a long time, and these systems are a long debated as they allow authorities to conduct dragnet surveillance on US citizens.
“The archetypical cell-site simulator, the Stingray, was trademarked by Harris Corp. in 2003 and initially used by the military, intelligence agencies, and federal law enforcement.” continues the post. “Another company, Digital Receiver Technology, now owned by Boeing, developed dirt boxes — more powerful cell-site simulators — which gained favor among the NSA, CIA, and U.S. military as good tools for hunting down suspected terrorists. The devices can reportedly track more than 200 phones over a wider range than the Stingray.”
The case of Marc Raimondi was also reported by The Intercept. Raimondi, who was employed by the Harris company and is now a Department of Justice spokesman, claims that the agency’s use of Stingray cellphone spying devices is legal.
Jennifer Lynch, a senior staff attorney at the Electronic Frontier Foundation, has waged a legal battle challenging the use of cellphone surveillance devices in a domestic context.
“We’ve seen a trend in the years since 9/11 to bring sophisticated surveillance technologies that were originally designed for military use—like Stingrays or drones or biometrics—back home to the United States,” said Jennifer Lynch “But using these technologies for domestic law enforcement purposes raises a host of issues that are different from a military context.”
Federal authorities have worked hard to not let the public know much about the cell-site simulators used by law enforcement.
I FIND ALL THIS SPY STUFF A COMFORT. WHY DO THEY MAKE STUFF TO SPY ON PEOPLE? LET US SEE NOW. THERE ARE PEOPLE WHO MAKE DRUGS THAT LITERALLY CAUSE PEOPLE TO LOSE THEIR MINDS, NOT TO MENTION CAN KILL. THERE ARE PEOPLE WHO BUILD BOMBS TO BLOW UP OTHER PEOPLE AS A HOBBY WHILE OTHERS MAKE BOMBS TO BLOW UP PEOPLE BECAUSE THEY THINK THEIR GOD WILL LOVE THEM MORE IF THEY RID THE EARTH OF THE EVIL PEOPLE THEY ARE KILLING. IT DOESN’T MATTER WHO THEY KILL OR WHAT AGE AS LONG AS IT IS THE ‘OTHERS’. AND THEN THERE ARE THE SPIES FROM OTHER COUNTRIES WHO COME HERE TO HELP CAUSE OUR COUNTRY TO BE TAKEN OVER. WE HAVE THE SLAVERS, AND THE SERIAL KILLERS, THE CREEPS WHO RAPE, TORTURE, AND ARE JUST ALL AROUND NASTY FOLK. THE ROBBERS AND THE DOERS OF DIRTY DEEDS. WE ARE SPIED ON IF SOMEONE DOES SOMETHING “THEY” THINK MAY BE A DANGER TO SOMEONE ELSE OR TO THE COUNTRY. OUR SOCIETY IS A SOCIETY OF CAMERAS. THEY ARE EVERYWHERE EVEN IF YOU CAN NOT SEE THEM, AND PEOPLE HAVE THEM ON THEIR PHONES AND CAN TAKE PICTURES, EVEN VIDEOS, AND DO AS THERE ARE VIDEOS EVERYWHERE ON THE MEDIA TAKEN BY THE AVERAGE PERSON TO SHOW SOMETHING SOMEONE HAS DONE. LOOK WHAT THE PRESS DOES. CATALOG OF SPY GADGETS? HA ! WE SPY ON OURSELVES TOO.
THE REAL SPY IS THE INTERNET, WHICH KEEPS TRACK OF ALL OUR INFORMATION , COLLECTING PIECES OF US EVERY TIME WE DO ANYTHING ON LINE TO SELL TO THE COMMERCIAL PEOPLE WHO WANT OUR MONEY AND THEREFORE WANT TO SELL US SOMETHING. EVEN THE SCHOOLS OUR CHILDREN GO TO SELL OFF OUR INFO TO MAKE MONEY. WE ARE THE BUYERS, THE SPENDERS, THE PEOPLE WHO KEEP MONEY FLOWING AROUND THE EARTH IN AN NEVER ENDING CASH FLOW SO THAT OTHERS MAY LIVE. WE ARE SPIED ON FROM BIRTH TO DEATH AND EVERYTHING IN BETWEEN. THIS IS PLANET EARTH. EVEN GOD SPIES ON US TO MAKE SURE WE ARE DOING WHAT WE ARE SUPPOSE TO BE DOING, AND I HEARD THE RUMOR THAT SANTA CLAUS HAS A PIECE OF US TOO.