The new online course offered by main ISIS noobs is based on Kali Linux
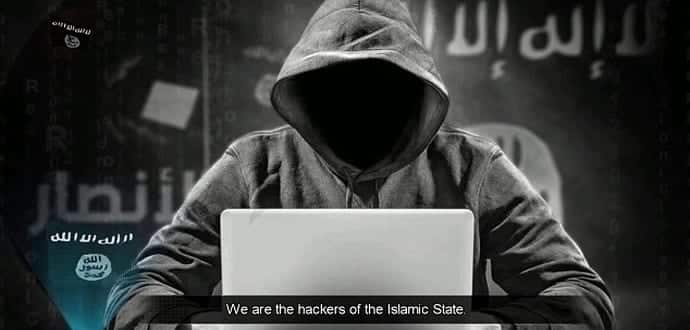
Looking to teach supporters how to “hack American and European security sites” and building a group of cyber soldiers associated with the terror organization, a member of al-Minbar, an active and influential online forum visited by ISIS supporters is now offering an online course on hacking tools, reports Vocativ. However, this is considered to be the latest in a series of miserable attempts by ISIS associations to bully cyber warfare on the West with little impact though.
The online course is based on Kali Linux, an open-source Linux distribution, which is a kind of operating system centred on Linux that consisted of hundreds of penetration-testing programs, which are created to help recognize vulnerabilities in an app or a computer network. A prominent member of the ISIS-sympathetic forum with the username ‘Ayam Fath Baghdad’ which means “the days of the conquest of Baghdad”, is the person behind the promotion of this online course.
He on Wednesday night wrote in Arabic, “As-salamu alaykum, my brothers, the members of al-Minbar, and those who are registered for the course on Kali Linux. Please gather in the section tonight at 9 p.m., Mecca time, in order to take a class.”
This user networks with at least other 25 members in the forum in a 20-page thread, all of whom show interest in taking the course and becoming hackers associated with the terror group. Based upon numerous Arabic-language YouTube tutorials, the course has been uploaded by a non-ISIS linked account. Online tutorials based on Kali Linux are abundant and freely available from a selection of online sources. Ayam Fath Baghdad offers advice on the use of the OS in order to supplement the YouTube videos.
“Kali Linux is known as the ‘go-to’ for black [hat] and white [hat] hackers alike,” Omri Moyal, VP Research at Minerva Labs, an Israeli cybersecurity company, told Vocativ over email. “It is widely promoted and educated in underground forums and anonymous chat rooms, and the combination of its pre-installed, ready-to-use, powerful tools make it extremely dangerous in the wrong hands,” he adds. “As we have heard that ISIS are declaring that they will move to operate in the cyber domain, it is very natural that they will go to this tool.”
However, there is no reason to panic immediately. Parts of the forum thread, including screenshots uploaded by the “students” and responses by the course’s teacher that were examined by Moyal told that the contents were “very, very basic material,” adding, “I can’t say anything about the teacher but the students are complete noobs.” The would-be hackers “have problems with the very basic commands and also are not looking for the solution themselves, something a good hacker must be able to learn and do,” his analysis mentioned.
Moyal emphasized on the fact that the complexity of the hacker themselves over the tools at their disposal, which, like Kali Linux, are normally readily available. He explained that while “the capabilities of Kali Linux are unlimited, it’s a tool box. The question is, ‘What are the skills of the person behind the keyboard?’”
According to Moyal, one of the methods offered in the course is an SQL injection, which “has the capabilities of extracting data from those databases. It is commonly used to deface websites and steal credentials.” Few years, a Saudi hacker had used a similar tool to steal thousands of credit card data from an unencrypted online database, explains Moyal. However, a hack of this nature requires extensive technical know-how and experience.
The aim of this online course is a grand finale in which students will carry out “join[t] attacks [by] the graduated members” and the group will build an ISIS-sympathetic hacking organization “along the lines of the United Cyber Caliphate (UCC),” referring to an online alliance of four ISIS-sympathetic, so-called hacking groups that was formed in late 2015. Then, ISIS supporters developed a channel on the encrypted-chat app Telegram devoted for “publishing courses of hacking and programming languages for the supporters of the Caliphate on the Internet.”
However, this newly formed group will not likely find much success, if it follows in the UCC’s footsteps. The UCC is incompetent, and their highest-profile “hack” involved just taking credit for others’ work, showed a study by Flashpoint, an intelligence firm.
The Caliphate Cyber Army (CCA), another ISIS-sympathetic “hacking” organization, which pre-dates the UCC and is now associated with the group, distributed a “kill list” lately that consisted over 4,000 names, addresses, and emails of individuals. On the other hand, the ISIS supporters claimed to have accessed the information via some kind of hack, Vocativ recognized a publicly available Excel file that includes the same details. Using search engines, the information was easily found and no hacking was required. Apparently, the CCA has figured out the information and just added menacing language, a propaganda plan designed to scare and threaten.
The online hacking course offered on al-Minbar is probably more or less the same. While the ISIS supporters may be eager to follow Kali Linux education, they do not have the technical expertise and background to likely be successful. It appears like ISIS supporters’ hacking threats once again are probably to remain just that: bullying by those with little capability to support them.
Source: Vocativ