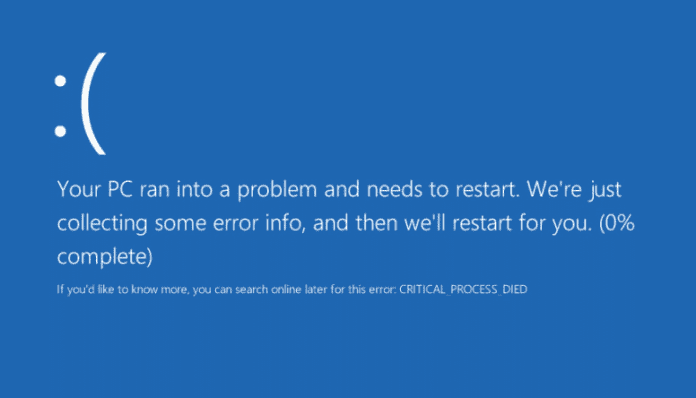
Rogue code on USB triggers BSOD on Windows PCs, even if it’s locked
Marius Tivadar, a malware researcher from BitDefender, a cybersecurity and anti-virus software company, has published a proof-of-concept (PoC) code on GitHub that can cause the dreaded Blue Screen of Death (BSOD) and crash the Windows machines within seconds, even if the system is locked.
According to Tivadar, the code exploits the vulnerability in Microsoft’s handling of NTFS (New Technology File System) images that can trigger a blue screen of death.
Explaining the PoC code on GitHub, Tivadar said, “One can generate Blue Screen of Death using a handcrafted NTFS image. This denial-of-service type of attack can be driven from user mode, limited user account or Administrator. It can even crash the system if it is in locked state.”
The malware researcher’s PoC contained a malformed NTFS image, which was stored on an USB thumb drive, which when inserted in a Windows PC crashed the system within seconds.
“Auto-play is activated by default,” Tivadar wrote in a PDF accompanying the POC’s GitHub project that detailed the bug and its effect.
“Even with auto-play [is] disabled, [the] system will crash when the file is accessed. This can be done for [example,] when Windows Defender scans the USB stick, or any other tool opening it.”
Autoplay, which is enabled by default in all versions of Windows, is the root of the problem here. Disabling Autoplay can prevent the NTFS image from automatically crashing Windows systems, but manually opening it has the same result.
According to Tivadar, the auto-play behavior should be changed in large part so it wouldn’t work if the Windows box was locked as the code runs without user consent.
“Generally speaking, no driver should be loaded, no code should get executed when the system is locked and external peripherals are inserted into the machine. I may think [of] this as code [that] gets executed without user consent,” he said.
He also suggested that an attacker might make changes to the PoC and add malware, triggering the crash remotely and opening “thousands of possible scenarios.”
Tivadar had reported the DoS (denial-of-service) attack to Microsoft in July 2017 and included the fake 10MB NTFS image that was able to crash Windows 7 and Windows 10 systems along with a PoC video.
Microsoft had responded to Tivadar’s PoC by saying, “Your report requires either physical access or social engineering, and as such, does not meet the bar for servicing down-level (issuing a security patch).”
According to Tivadar, when the vulnerability was disclosed, Microsoft said it did not want to assign a CVE to it. It did, however, write, “Your attempt to responsibly disclose a potential security issue is appreciated and we hope you continue to do so.”
Disappointed over Microsoft’s response, Tivadar published his NTFS image on GitHub recently. However, Microsoft is reported to have issued a fix for the Windows 10 vulnerability.
Source: Bleeping Computer