Apple, Amazon denies report of servers being compromised by Chinese spy chips
Chinese spying chips have been found on servers used by nearly 30 American companies, including Apple and Amazon, according to a Bloomberg BusinessWeek report on Thursday. However, Apple, Amazon Web Services and other involved companies have denied reports of being spied upon by the Chinese government.
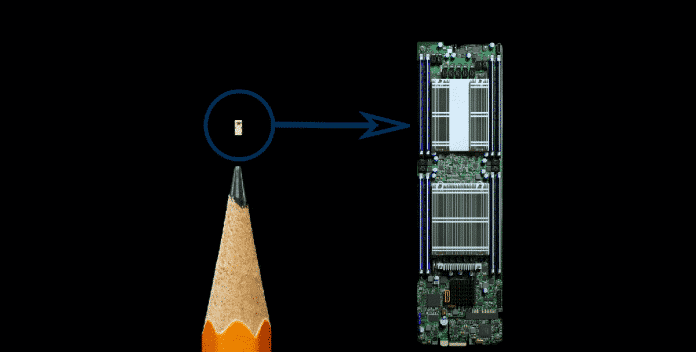
The tiny surveillance chip, which is not much bigger than a grain of rice, can bypass all security checks and give Beijing secret access to internal networks, Bloomberg BusinessWeek reported citing 17 unnamed intelligence and company sources.
According to Bloomberg BusinessWeek, a unit of the Chinese People’s Liberation Army intruded the supply chain of US-based computer hardware maker Super Micro Computer Inc to plant malicious chips that could be used to steal corporate and government secrets.
These malicious chips, which were not part of the original server motherboards, had been hidden on server motherboards during the manufacturing process in China. Further, these chips were disguised as signal conditioning couplers, to motherboards that ended up in US servers. Then, the infected motherboards were deployed by U.S. military, U.S. intelligence agencies, and many U.S. companies like Apple and Amazon.
“Apple made its discovery of suspicious chips inside Supermicro servers around May 2015, after detecting odd network activity and firmware problems, according to a person familiar with the timeline,” the report said.
“Since the implants were small, the amount of code they contained was small as well. But they were capable of doing two very important things: telling the device to communicate with one of several anonymous computers elsewhere on the internet that was loaded with more complex code; and preparing the device’s operating system to accept this new code.”
According to the publication, the chips were reportedly added to help Chinese government spy on American companies and their users, which is “more difficult to pull off and potentially more devastating, promising the kind of long-term, stealth access that spy agencies are willing to invest millions of dollars and many years to get.”
“Depending on the board model, the chips varied slightly in size, suggesting that the attackers had supplied different factories with different batches,” the report said.
During the same period, Amazon Web Services (AWS) too found the malicious chips. While the Bloomberg report states that both Apple and AWS notified the same to U.S. authorities, the above companies are claiming that none of it was found in reality and the infiltration never happened.
In regards to this, Apple issued a statement, which reads, “Over the course of the past year, Bloomberg has contacted us multiple times with claims, sometimes vague and sometimes elaborate, of an alleged security incident at Apple. Each time, we have conducted rigorous internal investigations based on their inquiries and each time we have found absolutely no evidence to support any of them. We have repeatedly and consistently offered factual responses, on the record, refuting virtually every aspect of Bloomberg’s story relating to Apple.
“On this we can be very clear: Apple has never found malicious chips, “hardware manipulations” or vulnerabilities purposely planted in any server. Apple never had any contact with the FBI or any other agency about such an incident. We are not aware of any investigation by the FBI, nor are our contacts in law enforcement.”
AWS also denied the report. “It’s untrue that AWS knew about a supply chain compromise, an issue with malicious chips, or hardware modifications when acquiring Elemental. It’s also untrue that AWS knew about servers containing malicious chips or modifications in data centers based in China, or that AWS worked with the FBI to investigate or provide data about malicious hardware,” the Amazon statement said.
“We’ve re-reviewed our records relating to the Elemental acquisition for any issues related to SuperMicro, including re-examining a third-party security audit that we conducted in 2015 as part of our due diligence prior to the acquisition. We’ve found no evidence to support claims of malicious chips or hardware modifications.”
Similarly, Supermicro also strongly denied Bloomberg’s findings and said in its statement, “While we would cooperate with any government investigation, we are not aware of any investigation regarding this topic nor have we been contacted by any government agency in this regard. We are not aware of any customer dropping Supermicro as a supplier for this type of issue.
“Furthermore, Supermicro doesn’t design or manufacture networking chips or the associated firmware and we, as well as other leading server/storage companies, procure them from the same leading networking companies.”