A team of cybersecurity researchers have developed a new sophisticated method of real-time listening in on private conversations by just observing vibrations in a light bulb hanging in a room.
Researchers from the Israeli’s Ben-Gurion University of the Negev and the Weizmann Institute of Science have dubbed the eavesdropping method as “Lamphone.”
This novel side-channel attack for eavesdropping sound can be performed by using a remote electro-optical sensor to analyze a hanging light bulb’s frequency response to sound through fluctuations in air pressure that cause vibrations.
To carry out the hacking tactic, attackers only need a telescope, an electro-optical sensor, and a laptop to extract sounds and speech from an individual in another location, says Wired, who were the first to report.
“We show how fluctuations in the air pressure on the surface of the hanging bulb (in response to sound), which cause the bulb to vibrate very slightly (a millidegree vibration), can be exploited by eavesdroppers to recover speech and singing, passively, externally, and in real time,” says Ben Nassi, a security researcher at Ben-Gurion who developed the technique with fellow researchers Yaron Pirutin and Boris Zadov.
“We analyze a hanging bulb’s response to sound via an electro-optical sensor and learn how to isolate the audio signal from the optical signal. Based on our analysis, we develop an algorithm to recover sound from the optical measurements obtained from the vibrations of a light bulb and captured by the electro-optical sensor.
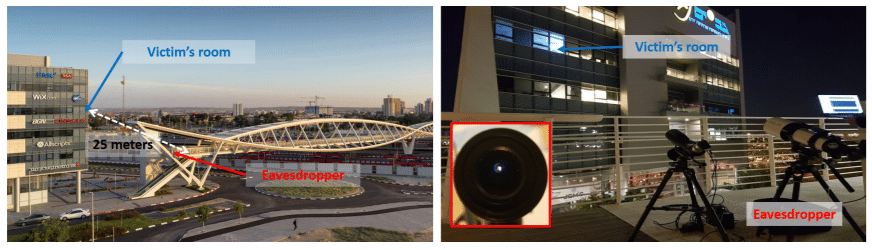
To test the performance of Lamphone attack in terms of its ability to recover speech and songs, the researchers positioned the eavesdropper on a pedestrian bridge approximately 25 meters (or 80 feet) outside of the target office window.
Using three telescopes with different lens diameters (10, 20, 35 cm) on the bridge, the researchers were able to recover the speech of Trump saying “We will make America great again”, which was played over speakers in the office room and accurately transcribed by Google text to speech API.
The researchers could also reproduce a recording of the Beatles’ “Let It Be” and Coldplay’s “Clocks” that was easily recognized by song identification services like Shazam and SoundHound.
According to the researchers, the maximum range to recover sound can be further amplified with proper equipment (bigger telescope, 24/32 bit ADC, etc.).
You can read more about the new attack in the “Lamphone: Real-Time Passive Sound Recovery from Light Bulb Vibrations” research paper, which will also be presented at the Black Hat USA 2020 conference later this August.