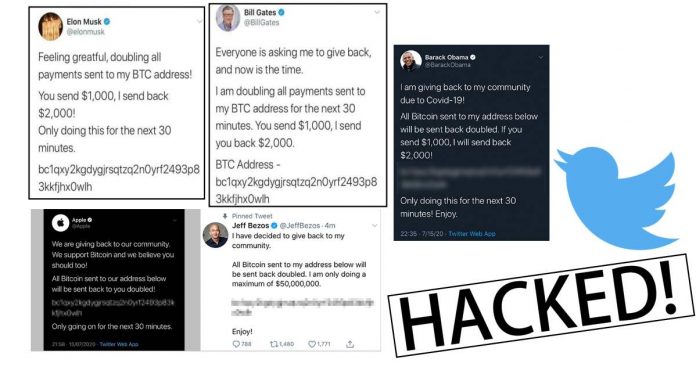
In a major high-profile Twitter hack, accounts of U.S. presidential candidate Joe Biden, Elon Musk, Bill Gates, Jeff Bezos, Barack Obama, Uber, Apple, and more, were compromised on Wednesday, in an apparent effort to promote a Bitcoin scam.
The tweet sent from hacked high-profile accounts urged their followers to send $1,000 in Bitcoin to a specific cryptocurrency wallet, with the promise that money sent would be doubled. The link to the Bitcoin wallet is consistent throughout all the tweets, suggesting a cryptocurrency scam.
Most of the accounts that were accessed in the scam had at least a million followers. The first known scam tweet was sent from Elon Musk’s Twitter account at 20:17 UTC on July 15, 2020.
The situation was first acknowledged by Twitter at 2:45 p.m. PT Wednesday afternoon, referring to it as a “security incident.”
We are aware of a security incident impacting accounts on Twitter. We are investigating and taking steps to fix it. We will update everyone shortly.
— Twitter Support (@TwitterSupport) July 15, 2020
Some of the tweets from hacked accounts were quickly deleted after they were posted, only to reappear minutes later.
As soon as the hack became viral, some verified users were restricted from posting new tweets from their Twitter accounts after the apparent hack.
Around 3:15 p.m. PT, the official Twitter Support account confirmed “[Users] may be unable to Tweet or reset your password while we review and address this incident.” By Wednesday evening, Twitter said that most accounts should be able to tweet again but functionality “may come and go”, as they continue working on a fix.
Most accounts should be able to Tweet again. As we continue working on a fix, this functionality may come and go. We're working to get things back to normal as quickly as possible.
— Twitter Support (@TwitterSupport) July 16, 2020
Jack Dorsey, Chief Executive Officer of Twitter tweeted late Wednesday that the San Francisco-based company was “working hard to make this right.”
“Tough day for us at Twitter,” Dorsey wrote. “We’re diagnosing and will share everything we can when we have a more complete understanding of exactly what happened.”
Security experts believe that the hackers ran the scam as a “smash and grab” operation: knowing that the intrusion into the accounts would be closed quickly. The hackers likely planned that only a small fraction of the millions that follow these accounts needed to fall for the scam in that short time to make quick money from it.
In the short time it was online, the Bitcoin address tweeted by the hackers has been sent over 12 Bitcoins, receiving hundreds of contributions totalling more than $110,000. The popular Bitcoin exchange Coinbase has blocked its users from sending money to the address.
While it is not immediately known how the account hacks took place, the hackers paid a Twitter employee as part of the scam, according to Motherboard who was contacted by at least four individuals claiming to be part of the scam.
The perpetrators presented Motherboard with screenshots showing that they had been able to gain access to a Twitter administrative tool that allowed them to change various account-level settings of some of the compromised accounts, including confirmation emails for the account. This allowed them or others involved to gain control of the account through password resets and post the tweets.
These hackers told the website that they had paid insiders at Twitter to get access to the administrative tool to be able to execute the scam.
“We used a rep that literally done all the work for us,” one of the sources told Motherboard. The second source added they paid the Twitter insider.
This information was validated by other security researchers who had been given similar screens, and tweets of these screens had been made. However, Twitter removed these since they revealed personal information about the compromised accounts.
Twitter later confirmed that the hack is “a coordinated social engineering attack” on employees that gave hacker “access to internal systems and tools,” which were then used to take control of high-profile accounts.
We detected what we believe to be a coordinated social engineering attack by people who successfully targeted some of our employees with access to internal systems and tools.
— Twitter Support (@TwitterSupport) July 16, 2020
“We’re looking into what other malicious activity they may have conducted or information they may have accessed and will share more here as we have it,” the company said on its support account.
Besides locking down the affected verified accounts, Twitter said they have also begun an internal investigation to find whether the employee hijacked the accounts themselves or gave hackers access to the tool. The company also have limited employee access to their system administrative tools as they evaluate the situation.