CD PROJEKT Red, the Polish video game developer best known for ‘The Witcher’ series and ‘Cyberpunk 2077, on Tuesday, revealed that they have been a victim of cyberattack due to which some of their internal systems have been compromised.
According to the game developer, an unidentified actor gained unauthorized access to the company’s internal network, encrypted all their servers and collected certain data belonging to CD PROJEKT capital group, and left a ransom note.
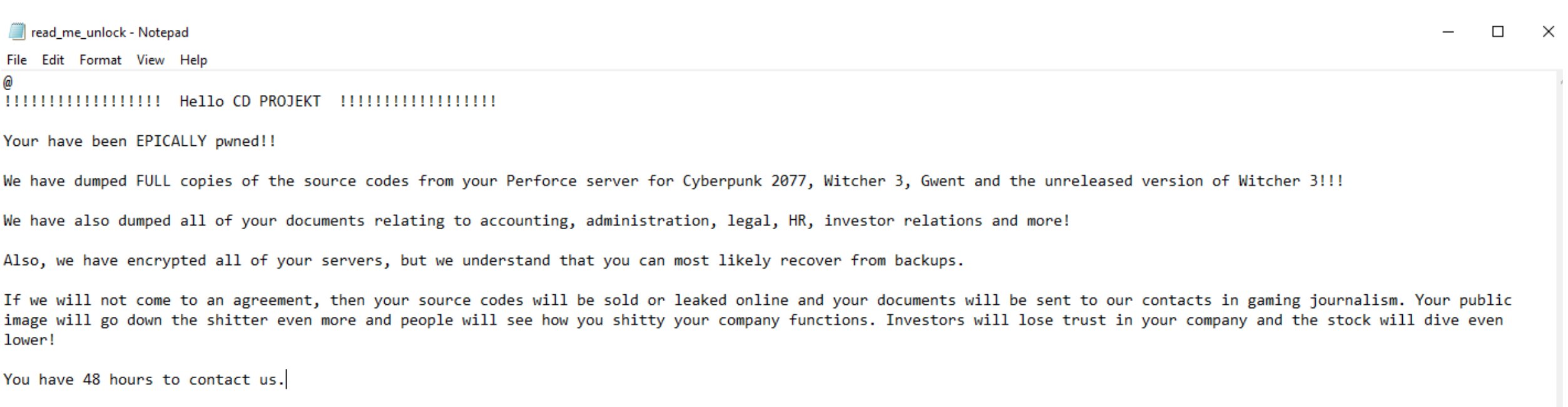
Below is the screenshot of the full ransom note left by the attackers for CD PROJEKT:
As one can see, the ransom note states that the hackers have full copies of source codes for Cyberpunk 2077, The Witcher 3, Gwent and the unreleased version of The Witcher 3, as well as documents relating to accounting, administration, legal, HR, investor relations and more.
The ransom note ends by noting that CD PROJEKT has 48 hours to contact the hackers for an agreement, or else they would leak or sell the source code online and send the documents to their contacts in gaming journalism.
CD PROJEKT said it won’t give in to the demands nor negotiate with the hackers, as the company is aware that this may eventually lead to the release of the compromised data.
“We are taking necessary steps to mitigate the consequences of such a release, in particular by approaching any parties that may be affected due to the breach,” CD PROJEKT said in its statement on Twitter.
The company said that although some devices on its network have been encrypted, backups of the encrypted devices are intact. It has already secured its IT infrastructure and begun restoring the data.
While CD PROJEKT is investigating the incident, the company confirms to its “best knowledge” that the compromised systems didn’t contain any personal data of its players or users of their services. It has already approached relevant authorities, including law enforcement and the President of the Personal Data Protection Office, as well as IT forensic specialists and is fully co-operating with them to investigate the attack.