Security Advisory released by Microsoft states that an attacker who successfully exploited the vulnerability could gain the same user rights and privileges as the current user using the machine. Which in essence means that if the victim is using a guest login, the hacker will have guest access to the machine but if the user is owner/or using the Administrative login and rights, the hacker will then have all the privileges the owner has. This can lead the a major security crisis.
A temporary patch has been released by the Company and can be downloaded here
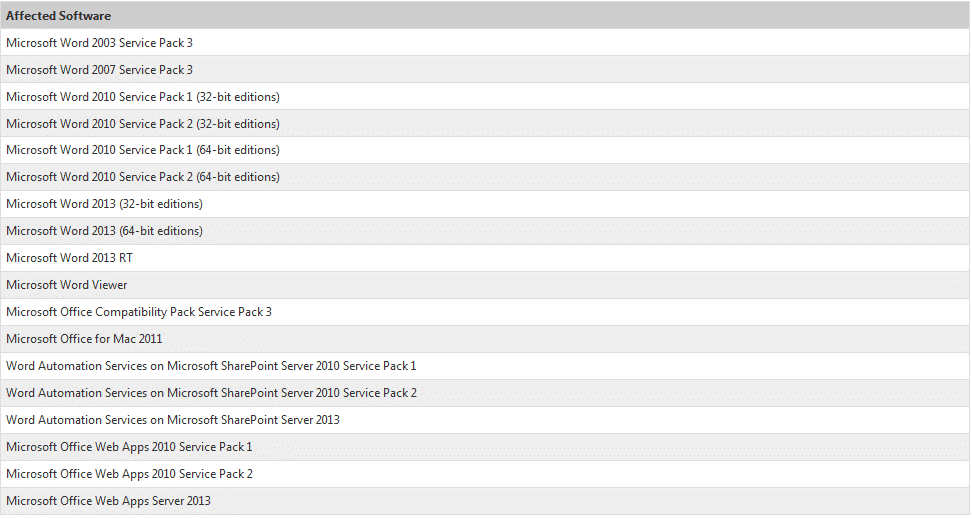 |
| (Effected Software Versions) |
While the temporary fix has been released by Microsoft but the exploit is still vulnerable for unpatched machines. If you are using Microsoft Word your maximum security lies in avoiding and not to opening or previewing an RTF email attachments from untrusted sources and websites.
Resource: Microsoft Security Advisory