Table Of Contents
8chan.co attacked with Lizard Stresser and knocked offline
After alleged DDoS of 4Chan, Lizard Stresser seemed to be at work in bringing down its competition, 8Chan.co.
The image boarding website which is popularly called infinite chan is currently under Distributed Denial of Service (DDoS) attack that is believed to be launched from the Lizard Squad’s rent-a-tool, Lizard Stresser.
As with alleged 4chan.org DDoS attack a few days back, only a tweet from the official Lizard Squad handle links the DDoS attack to the Lizard Squad’s Lizard Stresser DDoS tool. However this can be confirmed to originate from them as the tweet has not been deleted as of now.
https://twitter.com/LizardMafia/status/553099100686921728
8Chan was formed in 2013 and has been praised and panned for its very liberal views. It may not be as large as 4Chan but it has gained a lot of respect among the online community for its freedom of speech polity which allows which allows any controversial subject under the Sun to be discussed regardless of antagonism it creates. It rose to fame after the famous GamerGate controversy which revolved around the subject of sexism on video games. 4Chan admin had bluntly banned this particular thread as the discussion was thought to be particularly anti-feminist and misogynistic rhetoric, and have heightened discussion of sexism and misogyny in the gaming community.
8Chan however follows strict United States policies for copyright and visitors can create posts and reply to threads without registration.
CloudFlare not enough to stop the attack
When the ‘alleged’ DDoS attack on 4Chan was reported, many readers took exception that it had CloudFlare Content Delivery Network which could not possibly reveal the real IP address of 4Chan.
However now with 8Chan DDoS attack, CloudFlare seems to be not enough to tackle such kind targeted attacks.
CloudFlare CDN functions as a proxy therefore visitor requests for 8chan are passed through its network both for improving connection to the website and for analyzing them in order to protect against malicious activity.
As pointed above, the attackers seem to know the real IP address of 8Chan and have used this knowledge to contact the website’s server directly, eliminating any verification from a third-party service.
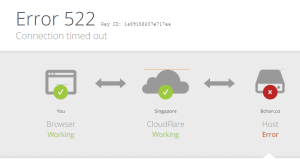
Trying to connect to 8Chan at the moment triggers a 522 error from CloudFlare service, indicating that no connection to the website’s server is achieved. Lizard Squad’s above tweet suggests that the renters of this particular attack have rented it for 24 hours.
Owner Fredrick Brennan stated that things should be repaired within next 12 hours but the actual time required may be much longer.
He also informed that if 48 hours pass and the issue is not fixed, he will launch a limited version of the image board on a different hosting service. Only a few boards would be available (/pol/, /v/, /gamergate/, /b/) and there would be no possibility for the visitors to create a new board.
“I am pretty confident it will not come to that, but it would be better to have something up rather than nothing if we know the real site is going to be down for a long time (72 hours – 2 weeks),” he said in a post on Pastie.
“Who is behind this? No one knows, and there is no way to know.Launching a DDoS is a crime, so attackers normally just rent botnets, use stolen credit cards to rent cloud servers, or pay someone in Bitcoin over Tor to do the attack for them to stay anonymous and not risk arrest.”
He added his own thoughts on the attack, “It took Lizard Squad attacking Microsoft and Sony for any of them to be arrested. Obviously, someone DDoSing a small community like 8chan.co is very low on the priority list for law enforcement.”
“Please do not believe rumors on Twitter that it was “Brianna Wu” or “Muslims” or “JIDF”. They are based on nothing and are being spread by people who want Twitter followers and nothing else. I verified it :^)”
The elaborate paste says that he is confident that 8Chan will be online soon.