Indian PC users being harangued by outbreak of TeslaCrypt Ransomware
Cyber experts have detected a new version of a notorious virus that is creating chaotic situation in India. This virus takes over the computer systems until money until a ransom in paid. Called ‘TeslaCrypt Ransomware’, the malware has been upgraded to the version 2.0.0 by the creators, is well known for infecting computers of gamers say experts. It also new encryption features and scheme, specifically to mimic CryptoWall.
The malicious program is now targeting businesses and online consumers via email attachments that does not allow access to a computer system until a sum of money, particularly in dollars, is paid as ransom. The ransom is doubled, if the victim delays in paying the ransom.
Detected in February 2015, TeslaCrypt grabbed headlines when it began infecting systems in the US, Europe and Southeast Asian countries. It then started in Indian cities including Mumbai and Delhi. Two businessmen from Agra were targeted in the last 6 months, from whom the criminals demanded ransom more than $10,000 to get their machines back.
Speaking to TOI, Agra cyber cell in-charge Nitin Kasan said, “In the last six months, two cases were reported in Agra, where the malware locked down its victim’s most important files and kept them hostage in exchange for a ransom to unlock it.”
Sandeep Gupta, a victim of online extortion, who owns a handicraft export company in Agra, said, “In February, my company website and emails which contained important transaction details and client information were blocked by some unknown Nigerian hacker.”
In an email, the hackers demanded a ransom of $10,000 (Rs.636,000) and threaten to destroy all of Gupta’s data. “I sought help from the Agra police cyber cell, who helped me to regain control over my website,” he said. The cyber cell helped Mr. Gupta obtain access to his website.
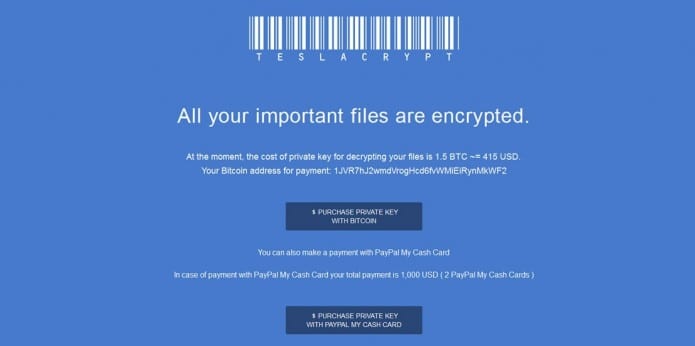
TeslaCrypt, also known as hunters of computer gamers, after getting control over the victim’s computer exhibits an HTML page on the web browser that is the same copy of CryptoWall 3.0, another well known ransomware program.
Altaf Halde, MD (South Asia) of Kaspersky Labs – a digital security agency – was the first to identify the malware said, “Ransomware is a type of malware that is a digital mechanism for extortion. The average consumer and both large and small businesses can be victims of ransomware. Such an attack is typically delivered delivered via an email that includes an attachment that could be an executable file, an archive or an image. Once the attachment is opened, the malware is deployed on the user’s system.”
It is interesting to know the way the TeslaCrypt malware functions. The recent version no longer uses GUI to inform users that their files are being encoded. A web page is opened in user’s browser due the malware, which displays a warning message. The message seems to be ‘friendly’ in nature that tells the user that their files have been ‘safely encrypted’. Users will need to open the File Decryption Site and then follow the instructions to decode all the files.
The Register informs that the malware has been able to generate about $76,500 (Rs.4,800,000) in just 10 weeks. Payable in Bitcoin, the TeslaCrypt asks for anywhere between $150 – $10,000 (Rs.10,000 to 630,000) It makes use of Tor anonymity network for all the communication, which makes it very hard to track.
Not opening the attachments from unknown sources is the only proven way to stay safe from TeslaCrypt and any other malware. Create backup copies of all of your essential files regularly. Copies must be stored on media which are bodily disconnected immediately after the backup copying is completed. Do not use borrowed pen-drives on your system, keep your anti-malware software up to date, and do not download anything from websites that are not trusted.
CryptoWall, CryptoLocker, CTB-Locker and CoinVault are all different variants of ransomware family.