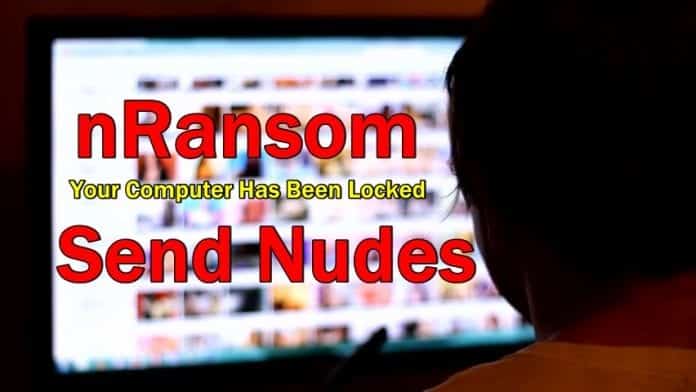
‘nRansomware’ demands victims to send nude pics instead of Bitcoin
Most of us are aware that ‘ransomware’ is a type of malicious software from cryptovirology that threatens to publish the victim’s data or perpetually block access to it unless a cryptocurrency—typically Bitcoin is paid. But what happens if you are asked to send nude photographs instead of Bitcoin to get access to your device? Shocked, right?
That is what a new ransomware known as “nRansomware” is doing. On Thursday, the researchers at MalwareHunterTeam, a research group focused on ransomware, discovered the ransomware software installed through a file called ‘nRansom.exe’, which demands ‘at least 10 nude photographs’ from the victim in order to get their files back. The victim is actually forced to create a Protomail account, which will then be ‘verified’ as legitimate by the attacker. Once the photos are sent, the victim will receive a code to disable the malware. It appears that the attackers are looking to sell the photos to make money.
The ransomware has a background of several images of the fictional children’s character Thomas the Tank Engine and an image stating the conditions. The malware also appears to play looped music in the background.
The below screenshot was tweeted by the researchers displaying the message when a victim’s device is hacked:
Not sure about this…
?
Sample: https://t.co/EOth6eUZOy@BleepinComputer @demonslay335
cc @x0rz @malwareunicorn pic.twitter.com/j5CAL2AH3Y— MalwareHunterTeam (@malwrhunterteam) September 21, 2017
“Your computer has been locked. You can only unlock it with the special unlock code,” reads the message. The victim is also asked to create an email account on a specified website and then email to hackers from that address. “After we reply, you must send at least 10 nude pictures of you. After that we will have to verify that the nudes belong to you.”
It is still unclear how many people have been affected with this ransomware or whether the demand is legitimate threat and not a prank. However, the file ‘nRansom.exe’, to some extent does appear to be legitimate, as it is classified as malicious by several antivirus engines, including VirusTotal and Hybrid Analysis, which are both public malware repositories.
To stay clear from these kinds of ransomware, it is always advisable to run supported version of an operating system and keep your device software up-to-date.
Source: Motherboard