Apple is automatically updating Macs to fix ‘root’ login vulnerability
Apple on Wednesday released an emergency patch that fixed an embarrassing login bug in its macOS 10.13.1 High Sierra operating system.
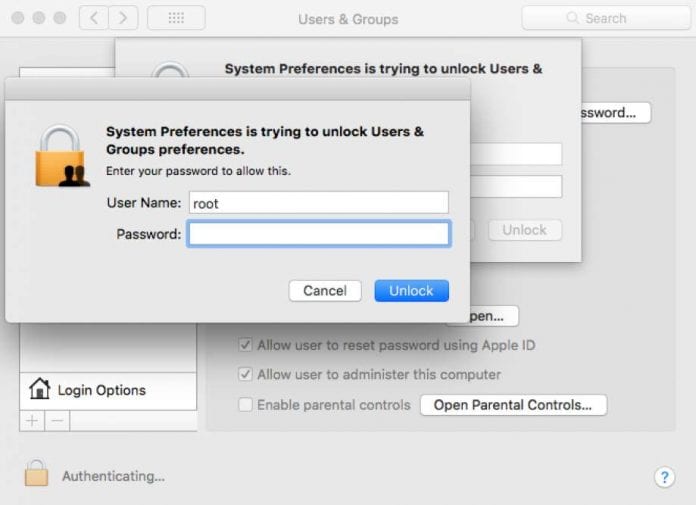
The vulnerability was disclosed by a user on Tuesday on Twitter. The flaw allowed a user to gain admin access to the PC without the owner’s password just by using ‘root’ as the user name and clicking the unlock button two times to get in.
The serious vulnerability has been identified as CVE-2017-13872, which has been fixed by Apple through Security Update 2017-001 for macOS 10.13.1 on Wednesday. While the security update is now available for download from Mac App Store, Apple said it will also be automatically installing the patch on all Macs running macOS High Sierra 10.13.1. However, if your device is running the 10.13.2 beta, you will likely have to wait until the next build is released.
Here’s the changelog:
Available for: macOS High Sierra 10.13.1
Not impacted: macOS Sierra 10.12.6 and earlier
Impact: An attacker may be able to bypass administrator authentication without supplying the administrator’s password
Description: A logic error existed in the validation of credentials. This was addressed with improved credential validation.
CVE-2017-13872
The build number for macOS should be 17B1002 after installing the new update, which is changed from 17B48. It does not require a reboot.
In a statement issued to MacRumors, Apple has apologized for the vulnerability:
“Security is a top priority for every Apple product, and regrettably we stumbled with this release of macOS.
“When our security engineers became aware of the issue Tuesday afternoon, we immediately began working on an update that closes the security hole. This morning, as of 8 a.m., the update is available for download, and starting later today it will be automatically installed on all systems running the latest version (10.13.1) of macOS High Sierra.
“We greatly regret this error and we apologize to all Mac users, both for releasing with this vulnerability and for the concern it has caused. Our customers deserve better. We are auditing our development processes to help prevent this from happening again.”
Source: Neowin