Table Of Contents
Developers turn to crimeware and release DroidJack RAT after their Android App failed to take off
Researchers at Symantec have been analyzing a new Remote Access Tool (RAT) for Android called DroidJack, which might have started out as an App on the Google play store. The developers whom Symantec has traced back to India, were apparently disappointed with the failure of the Google App to take off. The failure spurred them into the unintended world of crimeware and turned the App into a tool for cyber criminals.

Legitimate roots
Researchers at Symantec have been monitoring the evolution of the threat, which was first released in April 2013 on Google Play as Sandroid, a legitimate application for controlling PCs from an Android smartphone. But the App apparently did not catch the fancy of Android users and faded into obscurity. In late December last year, users spread news about the availability of a RAT tool on a hacker forum. This tool identified as SandroRAT McAfee was advertised to be an Android application that could be used to take control of smartphones from a computer. The SandroRAT was actually a full fledged Android Remote Access Tool which targeted banking users through phishing mail and stole their credentials. The ad, redirected the user to the app on the Play Store. This app was scrutinized by researchers when it started being spread via spam in the name of a Kaspersky security application. SandroRAT infected many a users in Europe especially Poland before it was brought to the notice of all concerned and taken down. However, SandroRAT is far from dead and buried.
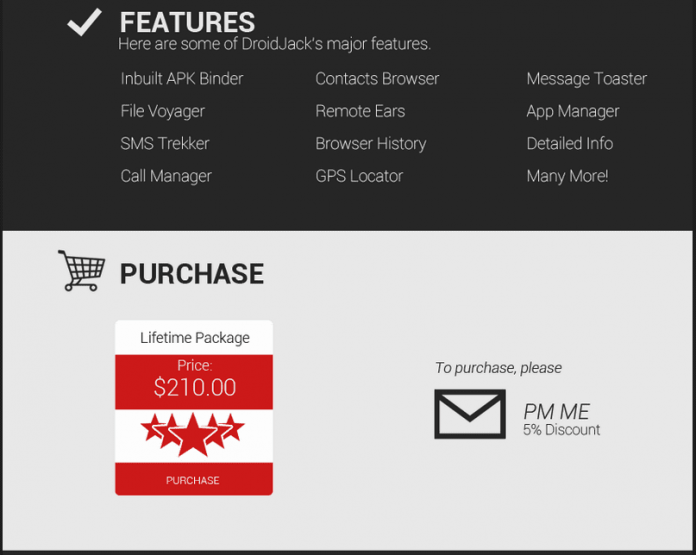
According to Symantec, DroidJack (detected by the company as Android.Sandorat) is the latest version of the SandroRAT. It was announced on June 27, 2014 on the same hacker forum and by the same individual who offered to sell SandroRAT. DroidJack is sold on its own website for $210, the cost of a lifetime package.
Indian Roots Traced
Researchers have analyzed the connection between DroidJack, SandroRAT and the Sandroid application and traced back their developers to India. “If the author or authors of DroidJack meant to cover up their tracks, they have not done a good job. Some simple investigations lead back to the names and telephone numbers of several individuals initially involved in the creation of Sandroid, supposedly based out of Chennai in India,” Symantec’s Peter Coogan wrote in a blog post.
Adding fuel to the fire, is a promotional video of the tool that shows the GPS pointing to a popular location in India. However, experts also note that there might be no real connection between the RAT and Sandroid, except the naming similarity. DroidJack is a sophisticated RAT that works without needing root access, and it can be packaged with any legitimate game or application. The tool can be utilized to harvest mainly banking details on the compromised device, install APKs, copy files to a computer, view messages, listen in on phone calls, list contacts, record audio and video via the microphone and camera, and get the phone’s GPS location.
Capabilities
DroidJack has similar features to other Android RATs, such as AndroRAT and Dendroid. Some of the more than 50 features on offer include the following:
No root access required
Bind the DroidJack server APK with any other game or app
Install any APK and update server
Copy files from device to computer
View all messages on the device
Listen to call conversations made on the device
List all the contacts on the device
Listen live or record audio from the device’s microphone
Gain control of the camera on the device
Get IMEI number, Wi-Fi MAC address, and cellphone carrier details
Get the device’s last GPS location check in and show it in Google Maps
The developers of DroidJack have included a disclaimer on their website claiming that they do not encourage the use of the application for illegitimate purposes, but this tactic doesn’t really work.
Other Cases
In September of this year, the creator of StealthGenie was indicted in the US. The creator – a Pakistani national – advertised the app as a means to spy on cheating spouses. Later they changed it to a parental monitoring tool claiming that users need to obtain written permission from the targeted individual.
Law enforcement agencies from all over the world are involved in operations targeting RATs. In May, 100 people were arrested as part of global raids targeting users of the BlackShades RAT.