Google Apps System leaks private information of over 282,867 protected domains exposing them to identity thefts and spamming
Google has leaked user information of some 282,867 registered domain users through the Google Apps system and the same is now publicly available, exposing it to risks ranging from spam to identity theft.
The Google Apps allows enterprises to purchase domain names from Google’s partners, while at the same time providing the App users with easy setup and associated services.
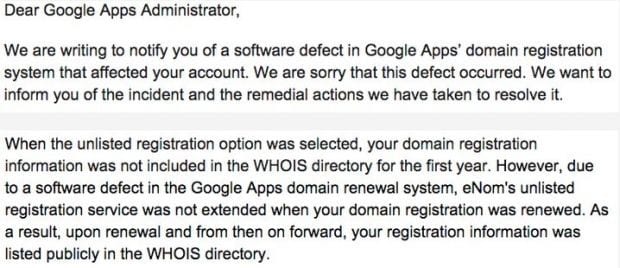
Announcing the leak in a email sent to the affected Google Apps users, Google said that the leak occurred due to a software defect. Google also said that its engineers were taking remedial action to contain the leak and details of those users who had renewed the domain services were affected by this leak.
As per ICANN rules all users who want to buy domains have make their identity, usernames, physical address, email ids or telephone numbers available in public.
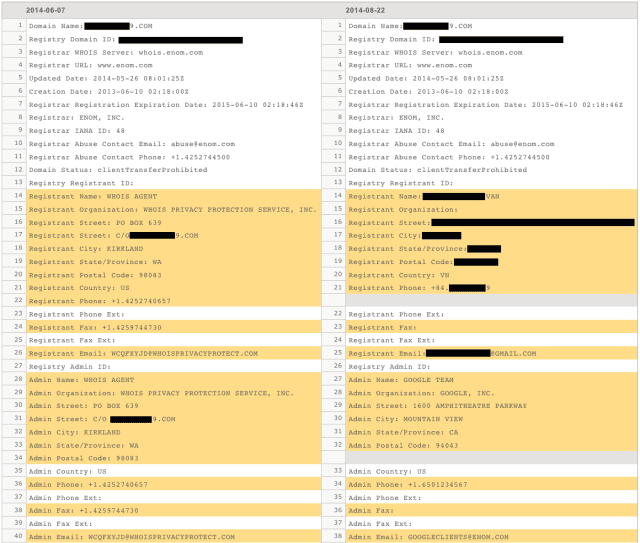
However, users can opt for a WHOIS privacy protection feature which is a premium service and lets them hide such details from public. This feature also helps such details from falling in hands of cyber criminals and being used for malicious purpose.
The Google Apps system leak affected such users who had opted for protected domain registration by paying extra money. Google said that inspite of opting for not including the details in WHOIS directory, the software glitch automatically made the details public.
“Due to a software defect in the Google Apps domain renewal system, eNom’s unlisted registration service was not extended when your domain registration was renewed.”
The domains have been registered through registrar eNom and security researchers said on Thursday that the number of records leaked represented about 94% from a total of 305,925.
Cisco Systems’ Talos researcher Craig Williams discovered the problem on February 19, 2015, and reported it to the Google Apps team. After conducting investigations into the matter, Google said told Williams that the issue had been resolved and only domains registered through its associate, eNom were affected.
It is to be noted that once such kind of information become public it is hard to erase it as well as protect identity thefts because the whois caches every single bit of data that is available online and anyone from any part of world can access it easily.
Williams, in a blog post said that such information can be easily used for malicious purpose. “For example, the domain ‘federalbureauinvestigations.com’ has an extremely poor web reputation score. Another domain, ‘hfcbankonline.com,’ also possesses a similarly poor web reputation score (we can only speculate as to the reason.)”
Williams also adds that the leaked data can be used by cyber criminals for spear-phishing the user, especially since the threat actor can increase credibility with valid information like phone number, addresses and real employee names.