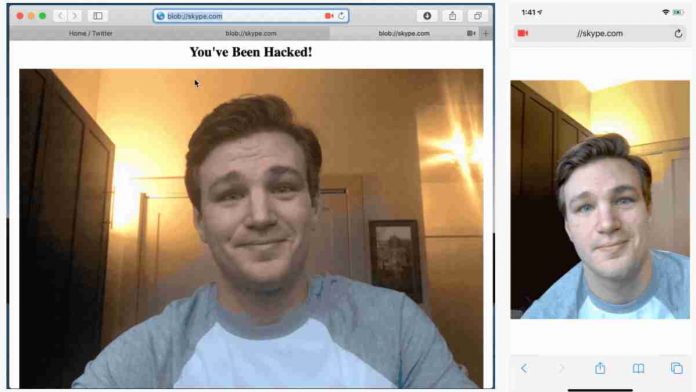
A former Amazon Web Services (AWS) security engineer Ryan Pickren, found seven zero-day security vulnerabilities in the Safari browser (CVE-2020-3852, CVE-2020-3864, CVE-2020-3865, CVE-2020-3885, CVE-2020-3887, CVE-2020-9784, and CVE-2020-9787), of which three of them allowed hackers to snoop into the camera of a Mac or iPhone when the user clicked on a malicious link.
According to Pickren, Apple requires nearly every app to be granted explicit permission to access the camera and microphone, but the same was not true for Apple’s own apps, such as Safari.
He exploited this exception to uncover the vulnerabilities and managed to “hammer the browser with obscure corner cases” until he got access to the camera.
“The camera security model in iOS and macOS is pretty intense. In a nutshell, each app must be explicitly granted camera/microphone permission, which is handled by the OS via a standard alert box”, Pickren wrote in a blog post.
“But there is an exception to this rule. Apple’s own apps get camera access for free. So Mobile Safari can technically access the camera without asking. Furthermore, new web technologies such as the MediaDevices Web API (commonly used in WebRTC transmissions) allow websites to utilize Safari’s permission to access the camera directly. Great for web-based video conferencing apps such as Skype or Zoom. But… this new web-based camera tech undermines the OS’s native camera security model.”
Pickren notified Apple about the seven vulnerabilities in mid-December last year, of which three of them (CVE-2020-3864, CVE-2020-3865, and CVE-2020-9784) were fixed by Apple in the Safari 13.0.5 update on January 28th.
The remaining four vulnerabilities (CVE-2020-3852, CVE-2020-3885, CVE-2020-3887, and CVE-2020-9787) that were considered as less severe were fixed in the Safari 13.1 released on March 24th, according to Forbes.
Pickren says Apple classified his method into “Network Attack without User Interaction: Zero-Click Unauthorized Access to Sensitive Data” category and awarded him a whopping $75,000 under Apple’s bug bounty program.
“The new bounty program is absolutely going to help secure products and protect customers. I’m really excited that Apple embraced the help of the security research community,” Pickren told Forbes.
If you are a Safari user, it’s recommended that you do not click on any malicious links on the internet.
Also, ensure that your web browser is up-to-date. Additionally, grant access to only those settings that are essential and keep camera permissions disabled by default on your PCs when not in use.