Hackers are having a field day with the tech giants. Last week it was Nvidia, and now Samsung has become the latest victim of a data breach.
The latest breach has resulted in the exposure of over 200 gigabytes of confidential data, which includes data of bio-metric unlock operations along with the source code for various technologies.
A hacking group, Lapsus$, has taken responsibility for the breach. They also were part of the Nvidia hack, which occurred last week.
The South Korean consumer electronics giant issued a media statement stating a “security breach” which exposed the internal company data with no risk to customer and employer data.
Table Of Contents
What’s at stake?
Lapsus$ posted details on their Telegram channel about the hack. It included the information about the breach and a torrent file for downloading the 190 GB file, containing source codes that expose the phone’s secure environment.
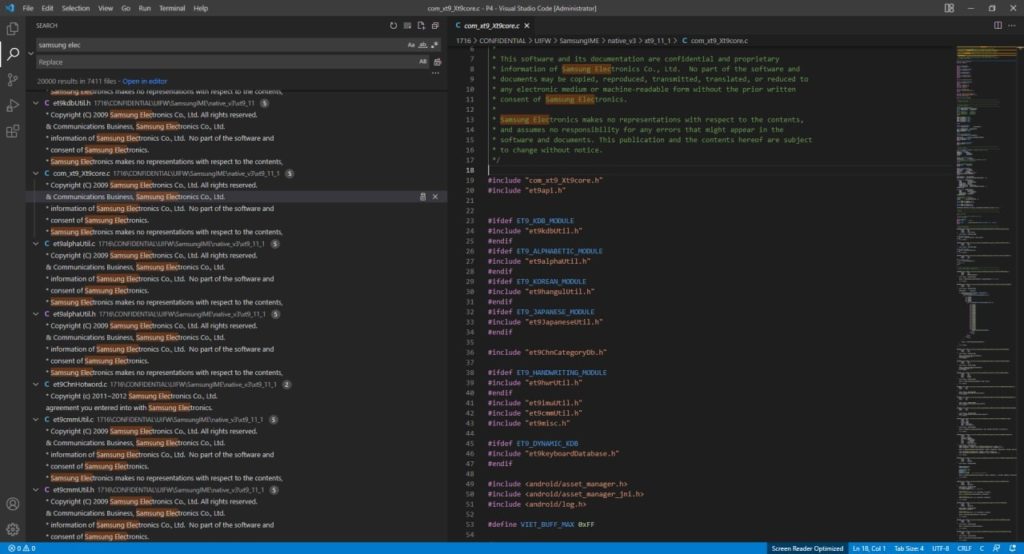
This could result in some comprise of the Samsung’s Trustzone environment, which the company uses on its phones for performing complex operations such as bio-metric unlock, and algorithms for boot-loader source code.
According to an independent analysis by Security Affairs, If Samsung’s signing key is leaked, there is a chance that the company cannot patch through updates to the devices without the risk of attack.
What is a Samsung Trustzone
Samsung has Knox, defense-grade security for its latest mobile devices. It leverages the processor architecture, ARM Trustzone, which creates a secure environment for confidential tasks. They include biometric unlock, updates, security key store, real-time security layer.
In easier, it is a secure zone for the device to perform tasks that are important to keep things n order without the risk of attack by malware hackers.

